Univention Blog
News, Tipps and Best Practices
Brief Introduction: Domain/Domain Controller
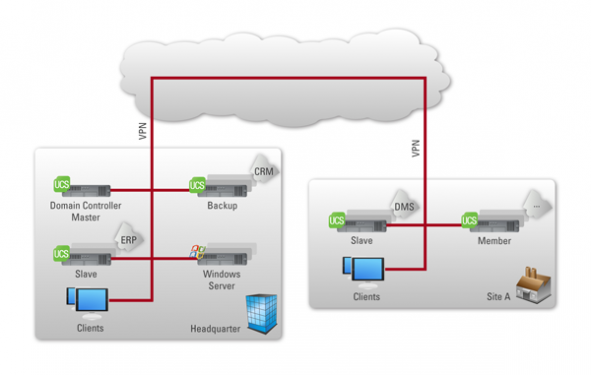
The terms domain and domain controller are often used when speaking about organizations’ IT infrastructures. But what exactly is behind these terms? Read our brief article, in which we use Univention Corporate Server to exemplify what a domain and a domain controller are and what functions they have.
Creating Trusts between UCS Samba/AD and Native Microsoft Active Directory Domains

In this article we would like to inform all IT administrators and IT-interested people about the possibilities of a trust between two domains (UCS Samba/AD and Microsoft AD). To set up a trust is to give users of one domain access to the resources of another. This can increase the scope for actions in some […]
Nextcloud for Private Clouds New in the App Center
Last week, at the didacta conference in Stuttgart, we announced that you can now install Nextcloud from the Univention App Center. Many users have been asking us about this as the need for a private cloud technology is big and Nextcloud offers the most security-focused and reliable solution in the market.
First milestone of UCS 4.2 Released
We are very pleased to present the first milestone of Univention Corporate Server (UCS) 4.2. The milestone is for our system house and technology partners, app providers and interested parties, who want to take a first look at the upcoming release of UCS. This milestone provides a preview of the new UCS portal, which makes […]
Brief Introduction: Differences of the Cloud Services IaaS, PaaS and SaaS
Summer time is conference time in the IT world and anyone going to one or more of these events hears about the latest developments in cloud computing, wondering sometimes how to keep up with the sheer number of cloud services acronyms used in this industry. So let us disentangle the secret code of cloud computing […]
How to Install Open Source SuiteCRM and Empower Sales

The core sales tool for every business in our increasingly data-centric world is customer relationship management (CRM). Your sales benefits greatly from CRM by collecting the best data of your leads. Likewise, marketing and general business planning also profit a lot from having the right information about customers and potentials. Using easy, web-based CRM tools, […]
OX in a Box: A Self-Contained Open-Xchange Environment for Containers and Virtual Machines

Container technologies like Docker make it possible for service providers to easily offer separated, private environments containing Open-Xchange and other services at a low footprint. But usually management of these services is a challenge. Univention provides a complete open environment to run and manage Open-Xchange inside Docker and popular hypervisors. This includes life-cycle, patch and […]
Secure Operation of Existing Applications in the Corporate Environment with Open Source Tools

Last year I submitted my Master’s thesis titled “Secure Operation of Existing Applications in the Corporate Environment with Open Source Tools”, and successfully earned my degree in IT from Bremen University of Applied Sciences. My research focused in particular on the differences and the security-related advantages/disadvantages of server virtualization compared with operating system virtualization, which […]
Univention App Center Provider Portal
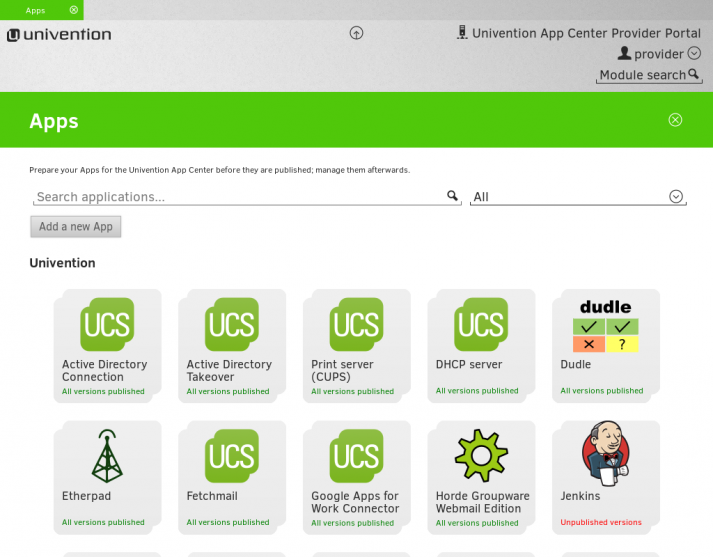
In the new App Center Provider Portal we have now developed an extremely convenient and contemporary tool for software providers looking to include their solutions in the Univention App Center and subsequently maintain them. The App Center is already home to more than 90 different apps developed for use in business IT, including groupware, ERP, […]
Introduction to the Univention App Catalog & UCS Appliances

The Univention App Center is an integrated part of UCS, our Open Source server and IT management software. With the integrated App Center UCS provides a central platform for the provision and integration of numerous enterprise applications. Find more infomation on the App Center and all available appliances at App Catalog. In the following video we introduce […]