From Practice
Univention App Highlights: Secure Network Access Control with RADIUS

Univention-App-Highlights: Secure and Centralized Authentication with Keycloak

Welcome to our fourth dive into the world of Univention apps! In this blog series, we regularly highlight exciting applications from our App Center. Today, we’re checking out Keycloak, an identity provider (IdP) that helps UCS admins manage user authentication and authorization in a secure and centralized way.
Univention Identity & Access Management will be called Nubus in the future

The Identity and Access Management (IAM) and portal, introduced as Nubus at the Univention Summit 2024, are already functional components of the Univention Corporate Server (UCS). To provide more clarity regarding our products, the Nubus product name will soon be visible within UCS.
Univention-App-Highlights: Self Service for Smarter Administration

Welcome to our third dive into the world of Univention apps! In this blog series, we regularly present exciting applications from our App Center. Today, we’re featuring the Self Service app – a tool that significantly lightens the load for UCS admins by delegating certain tasks directly to users.
UDM Blocklists: Take Control of User Properties in UCS Environments

Have you ever faced the challenge of ensuring certain user properties, like usernames or email addresses, remain off-limits for future accounts after deleting a user? The new blocklist feature in Univention Corporate Server Version 5.0-6-erratum-974 is the solution. This article takes a closer look at UDM blocklists.
Univention App Highlights: Enhancing Office Solutions Through Advanced IAM Integration

Welcome back to our journey into the world of Univention apps! In this blog series, we regularly present exciting applications from our App Center. In our second episoide, we’re diving into IAM integration with two key connectors: the Microsoft 365 Connector and the Google Workspace Connector. These apps build bridges and facilitate exchange between your […]
Univention App Highlights: Top 3 for Heterogeneous Environments

Welcome to our first journey into the world of Univention applications! In this new blog series, we will regularly present exciting applications from our App Center. In the first episode, we focus on three tools for different environments: Whether you’re using Univention Corporate Server as a single domain controller, integrating the server into an existing […]
A Strong Community – The Univention Help Forum

In today’s digital world, we depend more than ever on efficient and reliable software solutions to optimize our business processes and to modernize IT for education. At Univention, we offer solutions that meet the needs of our customers and users. But even the best software can occasionally raise questions or pose challenges.
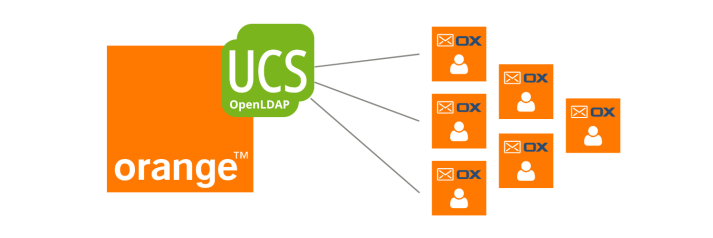
End of Migration: Orange Celebrated Successful UCS Project Completion
When we at Orange decided to renew our e-mail platform, we could not yet know that we would celebrate the successful end of migration on the 5th of July 2022 in our headquarters in Paris with more than 200 guests. We initiated the project back in 2014 and are now able to look back on […]
How the City of Schwäbisch-Hall Ensures a Sustainable Open Source IT Infrastructure with the Introduction of UCS

When people think of Schwäbisch-Hall, they most likely think of the building society of the same name or a picturesque old town (which is well worth a visit, by the way). Maintaining the latter is just one of the many tasks of the city administration. And the days of pencils and paper files are slowly […]