Univention Blog
News, Tipps and Best Practices
UCS 4.4: How to configure RADIUS
RADIUS (Remote Authentication Dial-In User Service) is a central component of UCS and enables you to control access to WLAN networks for users, groups, and devices. In January we published a blog post with a short introduction to RADIUS, and in this article I’m going to explain how to set up RADIUS for your UCS […]
Brief Introduction: DHCP and DNS
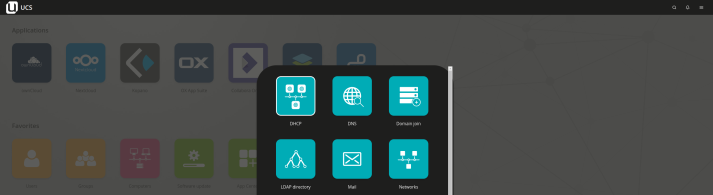
DHCP and DNS are two essential services in IT networks. While a DHCP server sends out information that clients need to communicate with other machines and services, DNS ensures that servers, clients, and services can be found by their names.
UCS 4.4 Release – Admin Diary, Self Services and Windows Domain Trusts
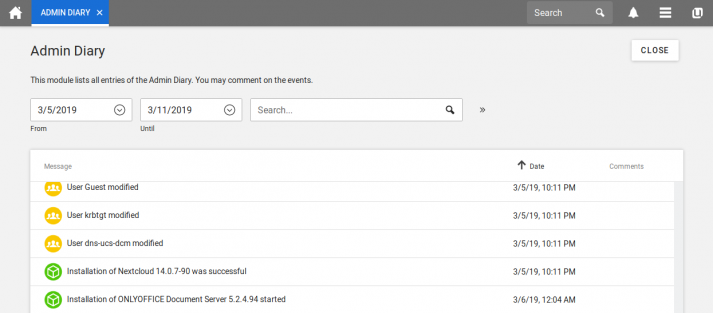
After the extensive updates of the basic distribution with the release of UCS 4.3, our focus during the development of UCS 4.4 was on the implementation of new functionalities: The enhancements include new functions in Self Services, in the Portal, in Radius Integration and in Services for Windows. In addition, the Admin Diary is a […]
Access your Desktop remotely with Guacamole

If you’re looking for a way to maintain your computers remotely, maybe Guacamole is the answer. The remote desktop gateway offers easy access to your systems – any time and from any location. All you need is a web browser: Guacamole is a HTML5 web application. Not long ago we’ve included the program in the […]
How-To: Single Sign-On for Nextcloud
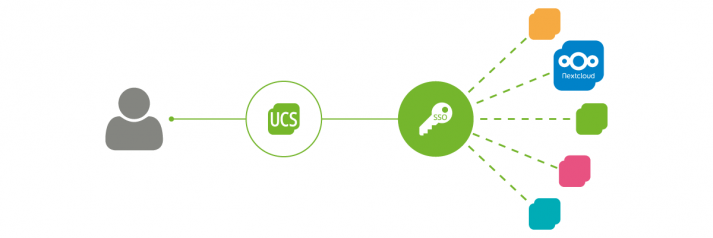
Log in once and automatically gain access to all programs and services – Single Sign-On (SSO) is a proven tool against the ever-increasing password fatigue among users. This is why many companies and educational institutions make it possible for users to log on centrally and only once. It is also easy to set up Single […]
Backup your Windows PCs: Bareos in the Univention App Center | Part 2
In February this year, we published a blog post on how to install the Bareos app via the Univention App Center. We explained how to modify the setup by adjusting some UCR variables and how to configure Windows or Linux computers from the UCS domain as Bareos clients. In this second part, we will explain […]
Linux and Windows Backups: Bareos in the Univention App Center | Part 1

In the App Center, our partner Univention provides a growing number of applications from different manufacturers. All programs can be installed and set up with just a few clicks. They’ve also integrated our Open Source backup solution: Bareos is licensed under AGPLv3 and specializes in heterogeneous IT landscapes. So, if you’re running UCS, the App […]
How-To: Securing Networks with RADIUS

Many organizations and educational institutions allow users to work on their personal laptops, tablets and smartphones. Bringing Your Own Device (BYOD) is popular because it reduces the financial burden on businesses and gives users a greater freedom of choice as well as their familiar working environment. Before users connect to the school or corporate Wi-Fi […]
Secure in the Cloud – Two-Factor Authentication for Single Sign-On

Today many services are offered as web applications. This can be self-hosted systems such as ownCloud or Kopano or cloud services such as the Google G Suite / Google Apps for Work. The number of services a user uses for his daily work is constantly increasing. So the desire for Single Sign-On is understandable. The […]
3rd Party App Charts in December

It’s time for a new edition of the 3rd Party App Charts. Compared to the last issue in September, there were the following changes: