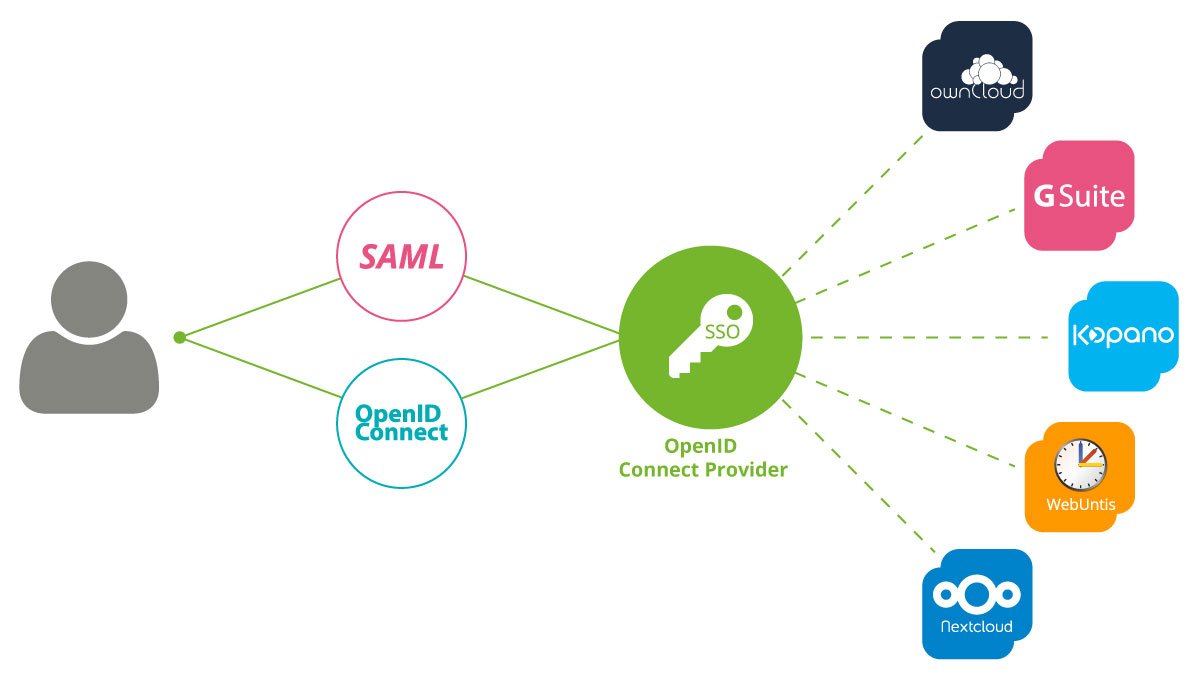
The integration of Kopano Konnect in the single sign-on network of Univention Corporate Server is an additional option for users to access a range of various applications that are integrated in UCS via a single, initial login using their user name and password.
The two authentication standards SAML (Security Assertion Markup Language) and OpenID Connect have already been available to UCS users for some time. So far, however, these two technologies have been two separated worlds. If some of the web services used SAML and others OpenID Connect for the authentication against UCS’ identity management, users were forced to log in twice in those environments with multiple services. With the support of the Kopano team, we were able to release an extension of the app “OpenID Connect ID” in the App Center. This is integrating the two standards with each other and thus allows a single authentication process by the end user.
I would like to briefly explain how a single sign-on generally works with UCS. Then I explain the interaction of Kerberos, SAML, and OpenID Connect and show you which functions the new implementation of Kopano Konnect offers to UCS users.
What Does “Single Sign-on” Mean?
With a single sign-on, the user logs on to the desktop computer in the domain and can then directly access other services such as file and print servers. The user only need to authenticate him- or herself once to an entity (server) (e.g. by entering a password or other factors) and then the SSO mechanism takes over the authentication against further services transparently in the background.
After the authentication, the user usually receives a data packet called ticket, token or cookie, which serves for a limited period (“session”) as an access key for authentication to the other services. The SSO mechanism stores the access key and ensures that the key is provided at the right time. Hence, the users only need to enter their user name and password once.
SAML and OpenID – Decentralized and Web-based Single Sign-on
OpenID and SAML are decentralized and web-based single sign-on systems, in which the users must have authenticated themselves with an identity provider (IDP) in order to subsequently access the connected services – so-called service providers (SP) – such as websites.
At the authentication service, the user’s browser receives a temporary session cookie with which he or she can access the integrated internal and external services. This process is secured by the signature of the session cookie, which is based on keys or certificates previously exchanged between IDP and SP.
Kerberos – Network-based Single Sign-on Protocol
Kerberos, in turn, is a single sign-on protocol that is designed in such a way that participating systems are connected in the same network. A client authenticates with the Kerberos server and receives a ticket (TGT – Ticket Granting Ticket). This ticket can then be used to call up additional tickets for various services.
Find out more about the three technologies in the article:
1 Password for All Services and Networks with Single Sign-on
Integration of the SSO Solutions SAML, Kerberos, and OpenID Connect
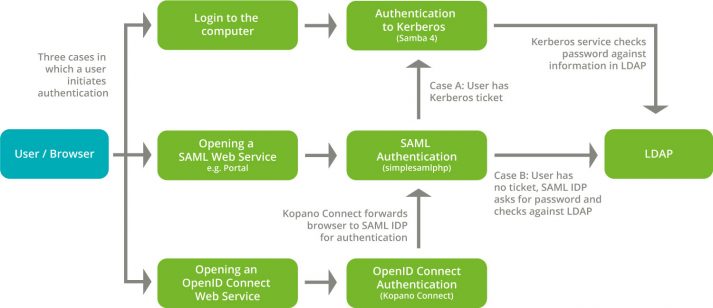
As described above, UCS has been integrating the Kerberos, SAML, and OpenID Connect standards for a while. The Kerberos login is part of the login to a system operated in the UCS domain, for example a Windows or macOS desktop. SSO via Kerberos then already allows simple access to servers in the internal network, for example to file and print services.
If a user has successfully authenticated via Kerberos (i.e.: he or she has already logged on to the workplace in the UCS domain and thus received a Kerberos ticket), the integration also allows direct access to web applications connected via SAML. You can find examples of this in various blog articles, for example, for single sign-on with Nextcloud, O365 or G-Suite. If the user accesses the service, the service asks UCS’ SAML identity provider (IDP) to authenticate the user. If the user already has a ticket from the Kerberos authentication, the browser sends this to the SAML IDP. This avoids having to re-enter the user name and password. As this feature is not standard, it must be activated by the UCS administrators.
OpenID Connect IDP Kopano Konnect as the New App in the Univention App Center
Since last week the OpenID Connect IDP “Kopano Konnect” has been part of this “single sign-on network”. You can integrate it into your UCS environment as a UCS app from the App Center. Does the user access a service that is configured against OpenID Connect, e.g. Kopano Meet, the OpenID Connect identity provider forwards the authentication request to the SAML identity provider in UCS. Here, the OpenID Connect identity provider takes on the role of the SAML service provider (SP). If the authentication against the SAML identity provider was successful, access to the connected service is granted. The SAML identity provider, in turn, can check the Kerberos ticket.
The processes are completely transparent to the user: The first access to an application prompts for authentication, then all applications are available. For example, directly after clicking on the UCS portal.
By integrating these various authentication protocols, Univention Corporate Server has taken another important step in the direction of a “hyper-integration platform”, as even more applications can now be operated even more conveniently and with continuous single sign-on without any technology break.

Comments
Felix Bartels (Kopano)
Hello,
the above blog already explains how SSO can be used with various clients (and it even works out of the box with Kopano Meet). We have create a small script for those that want to use SAML/OIDC with Kopano WebApp.
The script can be found at https://github.com/Kopano-dev/ucs-oidc-webapp/ and depends on git as the only additional dependency.