With the development of the OpenID Connect Provider App, which we announced at the Univention Summit 2018, we have taken another important step towards making UCS a secure and open platform for managing a wide range of services.
The goal we are pursuing: All UCS users should retain full control over their data and digital identities at all times. Also they should have the greatest possible and free choice between different software applications.
With this app, we are now offering an additional technology in addition to the SAML identity provider, which has long been integrated into UCS. They both allow administrators to connect third-party applications to UCS via single sign-on. The user authentication required for this runs against UCS’ identity management. The user password is not passed on to the connected service but remains in your system and thus under your control. The services to be connected must have an interface in order to work as OpenID Relying Party. The app is based on the software Konnect developed by Kopano, an OpenID Connect Provider developed in the programming language Go.
Single Sign-on with OpenID Connect and SAML
The use case for the OpenID Connect Provider is similar to the one of a SAML identity provider. The connected service does not receive the user password, but only the information that the user has successfully logged on to the identity management. For this purpose when using OpenID Connect or SAML, it is necessary to establish a trust relationship between the identity provider – in this case UCS – and the connected service before users can log on.
With SAML, a certificate pair is created and the public key is stored on the connected service. When using the OpenID Connect provider, establishing trust works in a similar way. Here, however, a shared secret is stored in UCS and the external service for communication. Another important difference between the two login procedures is that with SAML, all communication runs via the user’s browser who logs on to the UCS. With OpenID Connect, the initial login normally also runs via a browser. Afterwards the external service establishes a direct HTTPS connection to the UCS identity provider in order to query the required user attributes such as the name and e-mail address.
Connecting external services – Functionality of the App
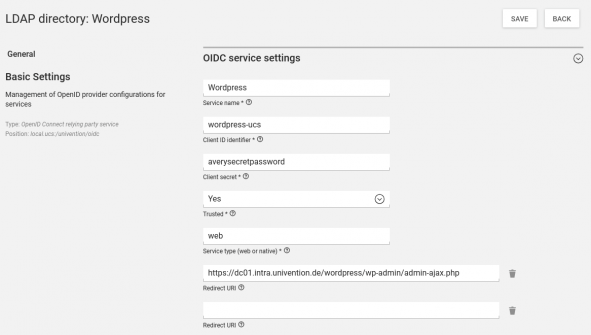
After installing the App from the Univention App Center you can connect external services to UCS via OpenID Connect by adding this service in the Univention Management Console in the LDAP browser in the containeroidc, which is located below the container cn=univention. Here you can register the new service by clicking on the button Add and selecting OpenID Connect Relying Party Service. The same is possible from the command line:
udm oidc/rpservice create --set name=<UCS_internal identifier> \ --position=cn=oidc,cn=univention,$(ucr get ldap/base) \ --set clientid=<ID> \ --set clientsecret=<A_long_Password> \ --set trusted=yes \ --set applicationtype=web \ --set redirectURI=<URL_from_Documentation>
nameis the service name displayed in the web interface during login.clientidandsecretmust be identical here and at the connected service (shared secret).trustedis set toyesif you do not want the user to be shown a separate request to confirm the transfer of user attributes. This should be set by default.applicationtypeis set towebfor Internet servicesredirectURIis the URL of the login endpoint found in the documentation of the connected service. If a service can be accessed via several URLs or should also be accessible via IP address, all possible addresses must be added to the attributeredirectURI.
The connected service needs information about the OpenID Connect endpoints for its configuration. These are available at the URL https://<FQDN of the server>/.well-known/openid-configuration.
Sample connection of WordPress to UCS OpenID Connect Provider
As an example, I will show you how to connect WordPress to the IDM of UCS as OpenID Relying Party. The WordPress App from the Univention App Center has to be installed in addition to the OpenID Connect Provider App. In this example both apps should be installed on the UCS DC Master to make the process simple.
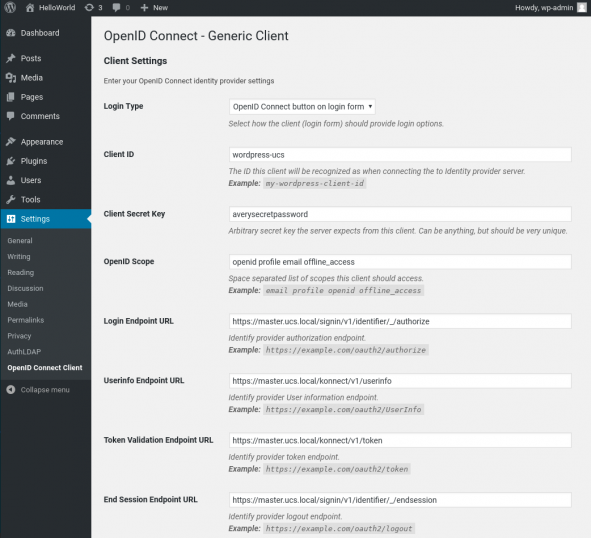
Now WordPress has to be prepared with a plugin for the login via OpenID Connect. The username of the WordPress administrator is wp-admin. The password can be found in the file /etc/wordpress-admin.secret. As an administrator, you can access the plugins menu in the WordPress administration interface via Settings. The Plugin OpenID Connect Generic Client can be found, installed and activated by performing a search under Plugins->Install. In the settings of the plugin the connection to the UCS provider must now be established. OpenID Connect Client is a new category under Settings. The UCS provider is added here. The settings are to be made as follows:
Login Type: OpenID Connect on login form
Client ID and Secret Key are freely selectable, but must be specified identically in the UCS configuration, see below. Scope defines the attributes the plugin needs from the UCS user.
Client id: wordpress-ucs secret: averysecretpassword Scope: openid profile email offline_access
The following fields should contain the corresponding values from the Well Known Configuration of the OpenID Connect provider, which can be viewed at https://<FQDN of the server>/.well-known/openid-configuration. A corresponding link can also be found in the UMC App description after installation.
Login Endpoint URL: https://<FQDN of the Server>/signin/v1/identifier/_/authorize
Userinfo Endpoint URL: https://<FQDN of the Server>/konnect/v1/userinfo
Token Validation Endpoint URL: https://<FQDN of the Server>/konnect/v1/token
End Session Endpoint URL: https://<FQDN of the Server>/signin/v1/identifier/_/endsession
Identity Key: name
Nickname Key: name
Email Formatting: {name}@mail.domain
Display Name Formatting: {family_name}
The Email Formatting item uses the username and a generic mail domain. The value {email} can also be set in the same field. In this case, however, it must be ensured that an e-mail address has been configured for the UCS users. Otherwise the login of the user will fail.
With a click on Save Changes, UCS is registered as OpenID Connect Provider in WordPress.
Now you have to make the WordPress configuration known in UCS. To do this, the options must be transferred via a terminal session. The values clientid and secret must be identical to the values entered above in WordPress.
udm oidc/rpservice create --set name=Wordpress \ --position=cn=oidc,cn=univention,$(ucr get ldap/base) \ --set clientid=wordpress-ucs \ --set clientsecret=averysecretpassword \ --set trusted=yes \ --set applicationtype=web \ --set redirectURI="https://$(ucr get hostname).$(ucr get domainname)/wordpress/wp-admin/admin-ajax.php"
This completes the setup and the access can be tested. An additional button ‘Login with OpenID Connect’ is now visible on the WordPress login page. On the OpenID Connect Provider login page the usual UCS user credentials can now be used. In order for the login to work smoothly, make sure that the WordPress login page is called via the FQDN of the UCS system, otherwise the redirection for users fails after authentication.
We would be pleased if the OpenID Connect App could offer you another good opportunity to expand your IT landscape with new applications that you can access easily and securely. Share your experiences and questions with us and other UCS users through the comment box below.
We are looking forward to your feedback. Further questions about the use of the app can also be asked in our forum.

Comments
Bobi
Hello, is there a way to get the memberOf LDAP property info OIDC token claim?
Bianca Scheidereiter
Hi Bobi,
no, unfortunately you cannot customize the list of submitted attributes with the current OpenID Connect app. There will also be no extension to the current app. We are currently working on providing Keycloak as a new OpenID Connect provider for as an app for UCS. Keycloak will then allow for much more granular control of submitted attributes. At the moment we can’t give an exact date when the Keycloak app will be available, but we are actively working on it right now.
Best regards,
Bianca