Whether it’s for access to the UCS portal, printers, or files, users’ authorizations in UCS are defined by their group memberships. This process facilitates the administration of authorizations in large environments in particular as there is no need to assign individual authorizations to each user separately. The group administration reduces the administrative efforts required when mounting new services to the central IDM especially if these services can be made available to defined groups in one go. Another considerable advantage is the fact that groups are saved in UCS’ LDAP and are thus identical across all UCS systems. In this way, you can not only tend to user accounts in groups, but also manage the authorizations of computer accounts.
 The “Groups” Module
The “Groups” Module
Groups are administrated in the “Groups” module, which can be found in the “Users” section of the UMC. The module allows you to create new groups, add users, and adjust settings.
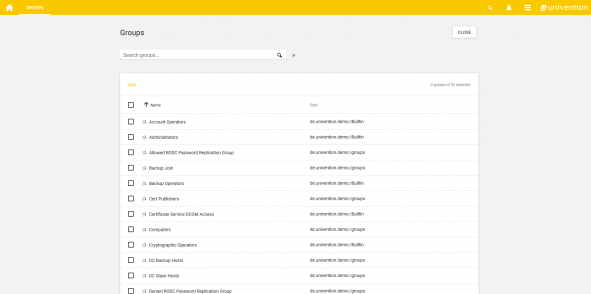
When you open the module, you are shown an overview of the system’s current groups. As you can see in the following image, UCS comes with a number of preconfigured standard groups.
Standard Groups in UCS
The authorizations and memberships are already preconfigured in the standard groups. For example, all of the domain users are members of the “Domain Users” group in the default setting. Members of the “Domain Admins” group have administrative access to the UCS servers.
There are also standard groups for servers in which authorizations are preconfigured, for example the “Domain Controller Backup” group. Each domain controller backup requires access to the SSL certificates on the domain controller master. In the standard setting, this access is controlled by making the DC backups members of the “DC Backup” group and granting this group access. This shows how groups can be employed to establish a trust relationship between the servers in a domain. The UCS Domain Join is another example of how standard groups can work together. In this case, an administrator must be a member of the “Domain Admins” and “Backup Join” groups.
If Samba 4 is installed, UCS also includes the standard groups required by Active Directory.
Creating a New Group
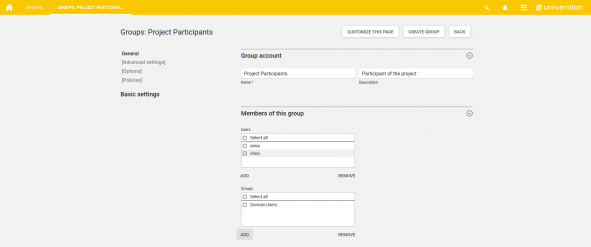
A new group can be created by selecting “Add” above the existing groups in the “Groups” module. You can then change the name of the group and add users as well as other groups on the “General” tab of the newly created group’s menu.
Generally speaking, it is possible to nest groups in UCS. For example, the “Technicians Site A” and “Technicians Site B” groups can be members of a superordinate “Technicians” group. This makes it very easy to establish cross-site and cross-school structures and hierarchies. You can also assign a group its own e-mail address, add computers, and change further settings in “[Advanced settings]”.
Defining Authorizations via Groups
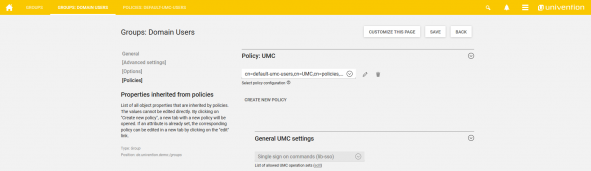
Another important element for the administration of groups is the defining of authorizations via policies in the “Policies” menu.
This shows you a list of all object properties that are inherited by policies. For example, UMC policies can be used to configure access to UMC modules. In this way, the administration of printers can be delegated to a “Helpdesk” group, for example.
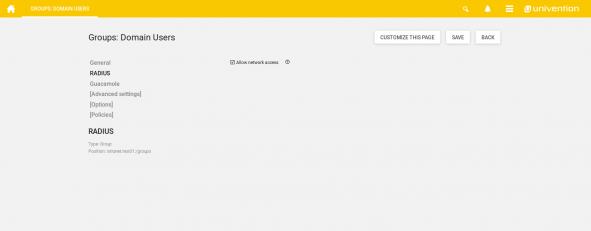
Authorizations and settings can also be determined via groups for applications such as ownCloud, Nextcloud, and other solutions integrated via the Applications or mounted via an interface. The screenshot below uses Radius as an example to illustrate how users in the “Domain Users” group can be granted network access.
As you can see, working with groups is an excellent solution for defining and administrating access authorizations for your users simply and conveniently. Together with the LDAP ACLs, UCS’ group concept lays the foundations for the configuration of authorizations in UCS.
Wanting more? The following articles might also be interesting for you: