In recent weeks, the increased demand for video conferencing solutions has kept us in the App Center team busy with the question of how Univention can help companies, organizations and school authorities to communicate effectively in digital form without leaving out aspects of data protection. For this reason, we have intensively studied various open source solutions for video conferencing and published quickly Jitsi Meet as an app in the App Center. It is now available to UCS users for easy installation.
Jitsi is a fully encrypted and 100% open source video conferencing solution. The connection to the UCS directory service via LDAP is already configured. Therefore, administrators of a UCS environment can give users access to Jitsi with their regular username and password using the Univention Management Console (UMC). Then Jitsi can be easily accessed from the UCS portal. In this blog post, I would like to show you the most important installation steps and then focus on the different use cases regarding user authentication. Organizations can use Jitsi Meet on Univention Corporate Server (UCS) to specifically control how open they make the access to the app and which users can conduct video conferences.
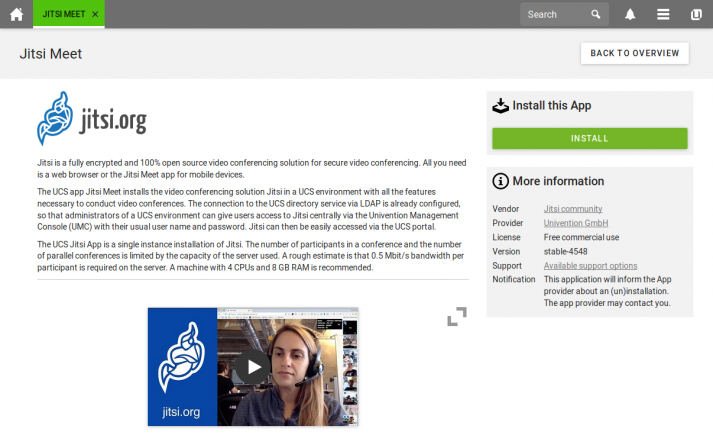
Installation of Jitsi Meet in UCS
Sufficient resources should be available for the installation of Jitsi Meet. 4 CPUs and 8 GB RAM are recommended by the Jitsi Project. Since all parts of Jitsi are installed on one system via the App Center a little more doesn’t hurt.
To install Jitsi Meet from the App Center, log in to the UCS management system of your UCS environment with your administrative user account belonging to the user group Domain Admins. Then open the App Center, go to Jitsi Meet and click Install.
If you prefer an installation via the command line, e.g. remote SSH login, all it takes is a simple univention-app install jitsimeet.
Technically, the Jitsi Meet app uses the official docker images of the Jitsi project and starts the services with a configuration adapted to the UCS environment.
Access Control of Jitsi Meet in UCS
After the installation, Jitsi is configured for guest access and for activated domain users.
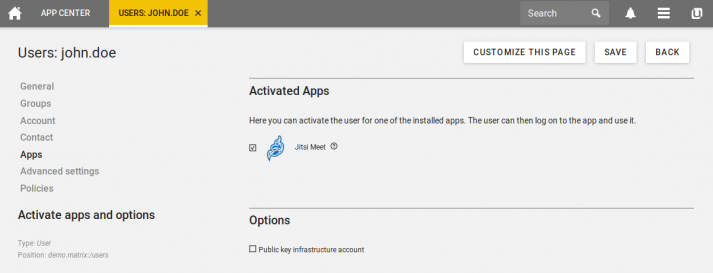
Users must be activated for the registration. To do so, open the user administration in the UCS management system, select the user and activate Jitsi Meet in the “Apps” tab.
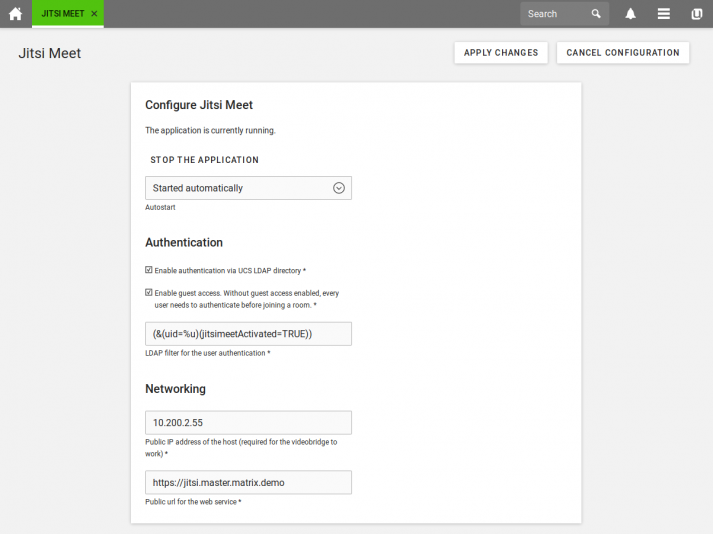
With the app settings for Jitsi Meet the following use cases for access control can be set.
Start and participation for every user
Every user is allowed to use Jitsi Meet independently from a user account. This setting is for organizations that want to offer video conferencing to any user regardless of whether they have a user account or not. If your Jitsi instance is accessible from the Internet, any visitor can conduct a video conference.
→ For this use case, disable the setting „Enable authentication via UCS LDAP directory“ in the app settings of Jitsi Meet..
Start and participation only for registered users
In this case, each participant needs a user account in your UCS environment to participate in a Jitsi video conference. This setting is useful if the system is accessible from the Internet, but should only be used by clearly defined users, for example if confidential topics are involved.
→ For this use case, disable the “Enable Guest Access” in the app settings of Jitsi Meet.
Only authenticated users start a conference
This is the default setting for a conference. Any user can join a conference, regardless of a user account. But only users with a user account can start a conference. This setting is suitable for organizations whose employees communicate a lot with external users for which an explicit user account should not be created.
→ For this case, enable the settings “Enable authentication via UCS LDAP directory” and “Enable guest access” in the app settings of Jitsi Meet.
The described setting options in the Jitsi Meet App on Univention Corporate Server (UCS) make a flexible spectrum of access control for video conferences possible. This makes it easier to communicate with external partners and can also be used in confidential contexts.

Comments
Mustafa
It was great, while it was very troublesome to add on other platforms, it is really easy for us to present this easily to us, it would be perfect if there were more than one language plugin, for example, Turkey (tr) …