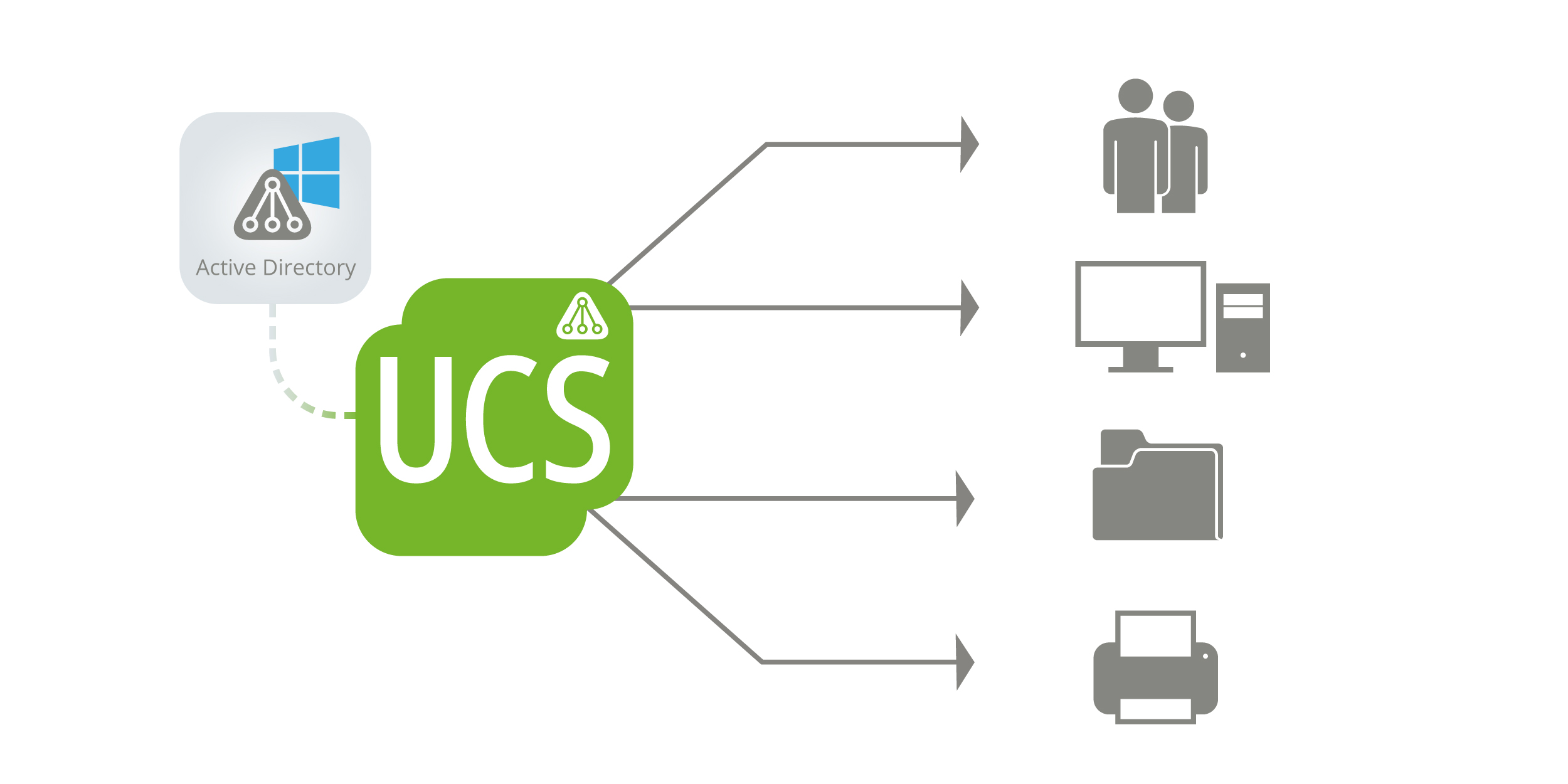
Our Univention App Center offers many open source applications from all areas, which you can add to your UCS environment in just a few clicks. Whether groupware, CRM or backup solution – the list of apps is growing continuously. If you want to use these applications in a Windows environment, UCS offers a particularly convenient way of doing so: UCS can be integrated with existing Windows environment, in particular, in an existing Active Directory domain.
After such an integration for which you use our app ‘Active Directory Connection’, the Active Directory (AD) continues to work as a the primary directory service, while UCS can extend the AD domain by exactly those open source software solutions that are available in the App Center.
Programs such as ownCloud, Nextcloud, Kopano or the Open-Xchange App Suite are thus also easily accessible to users of an AD domain. The administrative burden neither increases as UCS, being part of an AD domain, uses the AD‘s authentication services. You can thus eliminate managing your users twice.
In the following, I will explain to you briefly how to integrate UCS into an existing AD domain.
Two options for the UCS and AD domain: integration or synchronization
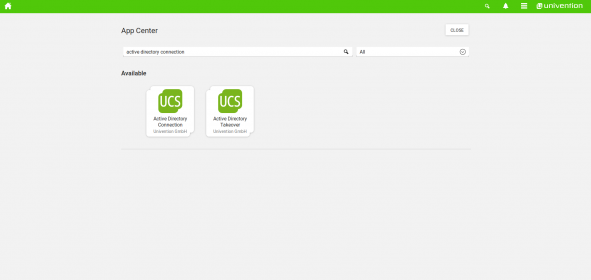
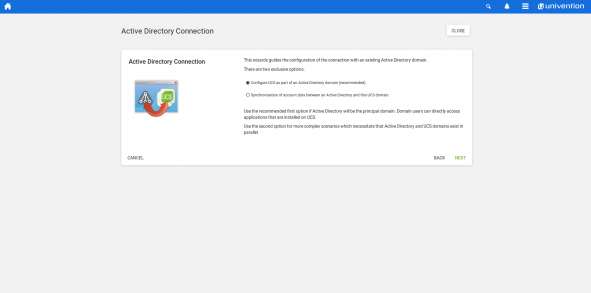
You‘ve got two option to integrate Univention Corporate Server in an existing AD domain. Our app Active Directory Connection helps in both cases:
- In the first case, UCS becomes a member of an AD domain (AD remains the primary directory service)
- In the second case, the AD and UCS domains operate in parallel. This setup involves the synchronization of all account data, but independent authentication mechanisms.
If the UCS server becomes a full member of an AD domain, UCS uses the AD‘s authentication services and makes them available to the open source programs from our App Center. The AD remains the primary directory service. The UCS server continues to provide the OpenLDAP-based directory services that are needed by the apps hosted in the App Center.
Alternatively, the App Active Directory Connection can synchronize users, groups, and passwords between an AD and a parallel UCS domain. This synchronization can happen uni- and bidirectional. Here, the authentication mechanisms work independently from each other.
Now I introduce you to the first scenario and explain how to configure UCS as a member of an AD domain. First of all, however, I would like to point out a few peculiarities.
Technical backgrounds – The role of OpenLDAP and Kerberos
The “member mode”, as we call this variant internally at Univention, includes some technical limitations. As UCS is not the leading identity management system in this operating mode, the Univention Management Console (UMC) protects user and group objects that are managed by AD tools against changes. In this case it will no longer be possible to reset users’ passwords via the UMC, because the password file does not exist in the OpenLDAP.
Please also note that the UCS server is not a classic domain controller in this mode. It is part of the AD domain and thus joined the Kerberos infrastructure deployed in the AD.
Set up UCS as an Active Directory member
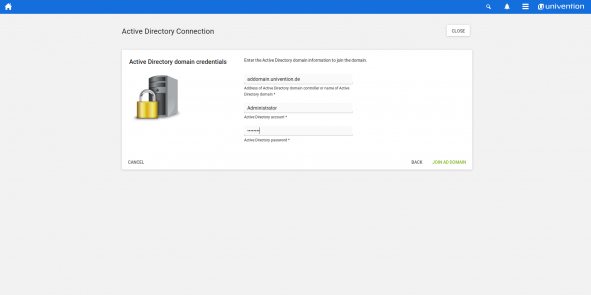
After the installation of the Active Directory Connection app via the Univention App Center, click on ‚Open module‘ and turn to ‚Configuration‘. Select ‚Configure UCS as part of an Active Directory domain (recommended)‘ if Active Directory is the main domain. Via ‚Next‘ you are guided to the input mask for the domain access data. In the top field you enter the IP address of the Windows server or the name of the AD domain. Below this is space for the username and password of an AD administrator account. Please note that this account must be authorized to create new servers and new users – a local administrator account for managing workstation PCs or end users is not enough. Afterwards click on ‚Join AD domain‘.
After a short moment you should see the message that the connection has been established successfully. The app’s configuration wizard also indicates that already connected UCS systems need to re-join the domain. Please do this for each UCS system by using the ‚domain join‘ module in the UMC of the respective server. Now you click on ‚Finish‘ and confirm the restart of the UMC server components and the web server.
The next time you want to log in, log in as an administrator, this time using the password from the AD domain. Once you successfully authenticated, you will see the Active Directory Connection module. It shows the status of the connection service and allows the set up of an SSL encryption and a password service.
Learn in this video, how you can operate a UCS system as a member of an existing Windows Active Directory domain via the App Active Directory Connection.
Way clear for a good cooperation across platforms!
Users, groups, and computers continue to be managed by the AD domain controller. Exceptions are attributes that only exist in UCS, for example, the activation or configuration of third-party apps like ownCloud, Nextcloud, Kopano, or Open-Xchange.
Thanks to the Active Directory Connection, you can extend your existing Windows domain by all functions of UCS. As a platform, Univention Corporate Server provides open-source applications for everyone – with the usual, convenient installation and configuration routines. If you have questions or suggestions, please visit us in our forum.
Further articles we can recommend
Brief Introduction: Samba / Microsoft Active Directory
Bye Bye Active Directory Password Service