Long before Samba became compatible with Active Directory (Version 4.0, 2011), the UCS AD Connector has already been implemented to build a bridge between UCS’ OpenLDAP-based identity management system and native Microsoft Active Directory domains. Indeed, the UCS AD Connector formed the starting point for the design of the S4 connector employed in UCS today internally to synchronize OpenLDAP with Samba/AD.
Or rather, we should say, it did so until recently, as it became apparent in two customer environments realized with UCS that the service was no longer able to write password hashes to AD for some user accounts, probably due to software updates on the Microsoft Windows domain controller. An analysis of the pwdump source code in the Development department at Univention identified the cause relatively quickly in an uninitialized element of an SAMR/DCERPC data structure, allowing the prompt resolution of the acute problem in both customer environments.
At the same time, the analysis unexpectedly revealed that the Microsoft Active Directory domain controller RPC interface employed in pwdump has to allow itself to be used directly from the AD Connector running under UCS even over an encrypted network connection. In a spontaneous event of enthusiastic joy of discovery, an unplanned but very constructive ping pong match of trial and error unwound between two of the Univention developers, which at the end of the day (or perhaps a little later) demonstrated the successful writing of password hashes to Samba via the SAMR interface with the help of Samba Python modules among other things.
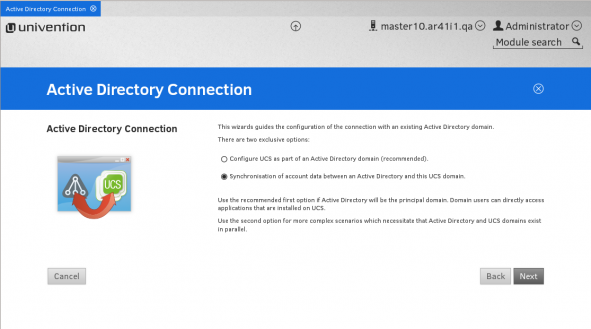
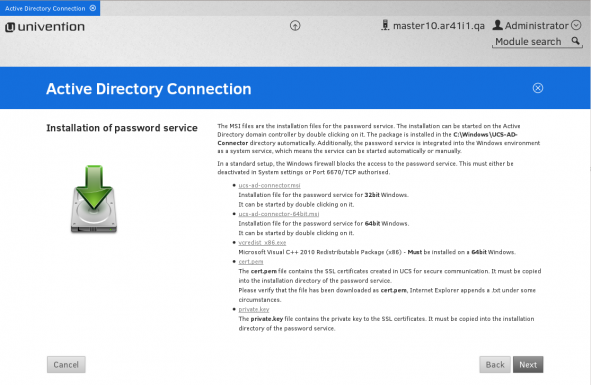
Seen by the light of day, a minor protocol adjustment was still required for successful communication with the native Active Directory, but the idea was born: Now if we were only able to realize the reading out of password hashes over an encrypted network connection, installation and testing of the UCS AD Connector would be considerably simpler, as it would no longer be necessary to install the special password service on the corresponding Microsoft AD domain controller. At the same time, removing this additional component, which previously had to be manually updated on the Microsoft AD domain controller following every update, would increase the security of the environment.
To the joy of the Development department, it took a relatively short time to identify this element of the functionality of the UCS AD Connector password service after a little research and have it independently verified by another developer and demonstrated as suitable for being put into practice with a prototype.
This spontaneous enhancement of the UCS AD Connector is good news for a number of reasons: On the one hand, the UCS AD Connector has enjoyed a second spring due to environments which run UCS as a member of a native AD domain as a convenient way of making UCS-based Open Source solutions available to Active Directory users by simply installing them from the UCS App Center. As the optional synchronization of password hashes to OpenLDAP is desirable for some of these apps, this new implementation of the password hash synchronization offers customers the advantages already mentioned above. On the other hand, it confirms that the expertise in Samba source code and the protocols used in Microsoft Active Directory collected at Univention over the years now allow themselves to be converted into actual solutions more and more frequently. In addition, it is a prime example of pure thrill of discovery, through which the further development of UCS also results in new benefits for UCS users time and time again.