Last week we added two new apps to the App Center: In addition to a connector for Google Apps for Work, there is now also a connector available for Microsoft Office 365. In today’s article, I hope to give you a brief overview of its advantages and explain the easiest way for you to configure and implement it.
You can find corresponding information on the connector for Google Apps for Work in this blog article.
Microsoft, Google, Open-Xchange – the list of suppliers offering browser-supported solutions just keeps on growing. Office products which are not installed on PCs, but run on the cloud instead, have two main advantages: They make working on the go particularly simple and they also save companies a considerable amount of administrative effort.
The tedious maintenance of license lists, the timely updating of the software on the individual workstations, incompatibility between products with different versions and the purchasing of licenses in packages which are either too big or too small are now all a thing of the past with online Office suites.
By integrating Office 365 in UCS, administrators can now save themselves the time-consuming creation of user accounts in the Microsoft administration interface. Thanks to the connector, they only need to place a check next to the user or user group in question in the UMC, and a Microsoft account is created automatically. The connector also brings with it extra convenience for users, as, thanks to the single sign-on (SSO) mechanism, they can log on locally with their usual password and then begin working online on the cloud immediately without any further action – their password remains in the company network and is not revealed to the cloud service.
For UCS to be able to provide Microsoft user accounts in the background without any intervention on the administrator’s part, it is necessary to configure a secure connection to Microsoft’s cloud in advance, or to be more precise: to Azure Active Directory (AAD). To make this easier for you, we have now developed a wizard which guides you through the entire set-up procedure step by step.
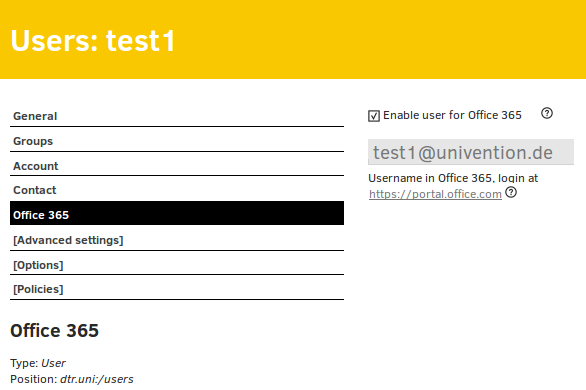
Once the configuration is complete, the administrator can select users in the Univention Management Console (UMC) and create Office 365 accounts for them, which they can then use without any further effort.
As of this point, selected account attributes of the UCS accounts are synchronized to the accounts on Microsoft’s cloud. The attributes to be synchronized (first name, surname, telephone number, etc.) can be configured by the administrator using the UCR. It is not only possible to configurable which attributes are synchronized, but also whether the values are anonymized, set statically to a certain value, or should be copied correctly.
Installation
The use of the Office 365 connector requires a Microsoft Office 365 administrator account, a corresponding account in AAD, and a domain verified by Microsoft.
The first two are provided by Microsoft free of charge for test purposes. However, the configuration of the SSO requires an individual Internet domain in which TXT records can be created.
If you don’t have an Office 365 subscription yet, go to www.office.com and select “Try it for free – For Business”. It is not possible to establish a connection to UCS with a private Microsoft account.
Log in to your Office 365 administrator account in the Office 365 Admin Center and select “Azure AD” in the bar on the left. A new window with the Azure Management Portal will open. You may need to fill in additional registration forms at this point.
You should now have your own Active Directory in Azure. Select it and go to “Domains”. You can add and verify your own domain here. To do so, it will be necessary to create a TXT record for your domain in the DNS. This procedure can take a few minutes.
Once it has been set up successfully, the status for your domain will be displayed as “Checked”. You can install the app in the App Center and start the wizard.
Use
The connector is ready for use as soon as the configuration is complete. Now, if you enable Office 365 for a UCS user account, a Microsoft account is automatically created for the same user and furnished with a license. You can view the use and assignment of licenses in the Office 365 Admin Center.
The users can now benefit from the single sign-on mechanisms in UCS. The username to be entered for the Office Portal is visible for enabled UCS users in the “Office 365” tab. Once you’ve entered the username, you are forwarded on to the UCS single sign-on page. There, the users can log in with their UCS login data and are automatically forwarded to the Office environment, where they can start working directly. The user password is thus not revealed to Microsoft. It’s even quicker, more reliable and simpler if you allow your users to start on the overview page of your UCS server.
From there, they can access the UCS single sign-on page with a mere click of the mouse and thus avoid having to input their username twice.
One-way-street
The connector only works in one direction: Users are synchronized from UCS to the Microsoft directory. Changes to users which are made in Azure AD or the Office Portal can be overwritten with changes to the same attributes in UCS and therefore by the connector under certain circumstances.
Unfortunately, due to new security policies at Microsoft, it is not possible for the connector to delete any users or groups in Azure AD. As such, if the Office option in UCS is disabled, they are merely disabled and renamed. All licenses are returned so that they are then available for other users and no extra costs arise. You can simply delete users and groups whose names begin with ZZZ_deleted_ in the Office 365 Admin Center.
Configuration
Microsoft demands to know in which country the users of the Office 365 service work. The connector determines this by using the data entered for “Country” in the user’s contact information or, if no data is available, the server’s settings. It is also possible to specify a 2-character abbreviation such as DE across the board using the UCR variable office365/attributes/usageLocation. For legal reasons, we recommend setting this variable.
Corresponding accounts are created in the Microsoft directory for the UCS user accounts for which Office 365 is enabled and selected account attributes synchronized with them. A range of UCR variables can be used to configure what data should be synchronized.
The UCR variable office365/attributes/sync is used to configure which LDAP attributes (e.g., first name, surname, etc.) of a user account are synchronized. This is a list of LDAP attributes separated by commas. Remove the attributes from the list that you do not want to synchronize and empty it completely to synchronize nothing but the username.
Changes to the UCR variables are only implemented the next time the listener is restarted: invoke-rc.d univention-directory-listener restart
Advanced configuration
The UCR variable office365/attributes/anonymize can be used to enter LDAP attributes separated by commas, which are saved for Microsoft but completed with random values. The UCR variables office365/attributes/static/.* allow the completion of attributes at Microsoft’s end with a preset value.
The UCR variable office365/attributes/never can be used to specify LDAP attributes separated by commas, which should never be synchronized even if they appear in office365/attributes/sync or office365/attributes/anonymize.
The UCR variables office365/attributes/mapping/.* define mapping of the UCS LDAP attributes to Azure attributes. These variables do not normally need to be changed. You can enable the UCR variable office365/groups/sync to synchronize the groups of users enabled for Office 365.
If you experience any difficulties, checking the log file can often be helpful. Enabling of the UCR variable office365debug/werror elevates debug tasks to the “Error” class and records them in /var/log/univention/listener.log.

Comments
TJ Chen
Hi,
How do I fix the setup wizard error message below?
An error occurred
Could not fulfill the request.
Server error message:
Error reading token received from Azure. Please run the wizard again.
Daniel Tröder
Hello TJ Chen,
the error can have multiple causes. Please retry and post the new and relevant content of the logfile (/var/log/univention/management-console-module-office365.log) at the forum, so we can work on a solution: https://help.univention.com/c/ucs