We reached an important milestone in the step-by-step migration to Keycloak as an Identity Provider in UCS: In August 2022, we made Keycloak available as an app in the UCS App Center for integration in UCS in an initial version and have improved it ever since. With the latest release in December, the app is now also part of our official product support, and thus ready for productive use.
In this article, I would like to give you an overview of the possibilities that Keycloak will offer you, the current status of the migration of the Identity Provider from UCS based on Keycloak, as well as an outlook on further features yet to come in the next few months.
Table of Contents
What functions does the Identity Provider offer?
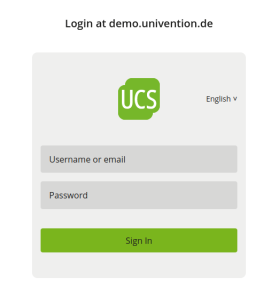
The Identity Provider (IdP) handles authentication and, optionally, authorization of identities that want to access IT services. For authentication, the Identity Provider checks whether correct credentials are available – in the case of a user, for example, the user ID, password and, if necessary, other factors – and can then decide which services the person is allowed to access (authorization). To ensure that the process remains convenient for users, the Identity Provider implements single sign-on technologies such as SAML or OpenID Connect, which enable one-time authentication with the same credentials to access many services.
How is the Identity Provider currently provided by UCS?
UCS has long supported the SAML (Security Assertion Markup Language) and OpenID Connect protocols for single sign-on to web applications. For this purpose, we have integrated the software solutions “simpleSAMLphp” and “Kopano Connect” into UCS. These offer good and deep integration with UCS user management (Univention Directory Manager) and the Identity Store (OpenLDAP), but compared to other implementations, the configurable range of functions is limited.
Therefore, after comparing different open source implementations for identity providers, we decided to perform a step-by-step migration to the Keycloak software as the new Identity Provider and set it as the future standard in UCS.
Keycloak is much more extensively configurable than the previous Identity Provider and comes with many additional functions that we have gradually activated and will activate in UCS. Keycloak is used by a large number of organizations worldwide and is therefore also being developed much more actively than the previously integrated solutions, which have stagnated or even been discontinued.
What functions should UCS with Keycloak offer in the future, and where does the current app stand?
The feature set of Keycloak is very extensive and extensible through plugins and APIs. The current feature set of the UCS Keycloak app provided in the App Center already significantly exceeds the scope of the old IDP, but for a replacement in all previous deployment scenarios some functions are still missing. We therefore plan to continue developing the app step by step before it will eventually replace the previous IDP completely as a new standard.
In the following table, I provide an initial overview of the existing and upcoming features of the Keycloak app and compare their current implementation status to the functionality of the old IDP.
| Functionality | Implementation Status Keycloak App | Available for previous IDP (SimpleSAMLPHP / Kopano Connect) |
| Single sign-on via SAML and OpenID Connect | Implemented | Implemented |
| Redundant operation on multiple UCS instances | Implemented | Implemented |
| Integrated 2-factor authentication (OTP) | Implemented, but not yet in scope of support | Not available |
| Advanced 2-factor authentication via PrivacyIdea | Implemented, but not yet in scope of support | Implemented |
| Identity Federation for external IDPs and their service providers | Implemented, but not yet in scope of support | Limited availability |
| Identity federation for service provider provisioning on UCS for external IDPs | Implemented, but not yet in scope of support | Not available |
| Single sign-on with Kerberos for workstations in UCS Kerberos/Samba domains | Not yet implemented | Implemented |
| Brute Force Login prevention (Abweisen extrem häufiger Anmeldeversuche) | Under implementation | Limited availability |
| Configurable login mask (theme, links) | Under implementation | Implemented |
| User guidance for expired passwords and for onboarding after self-service registration | In planning | Implemented |
The exact description of the functions – especially the Identity Federation – would go beyond the scope of this blog article. We will go into this in more detail in further blog articles.
In general, a native Keycloak offers even more possibilities than are currently usable in the app for UCS. The exact status of the current version of the UCS Keycloak app can be found in the UCS documentation, as well as information about the range of functions covered by our support.
When will the Keycloak App become the new default IDP?
We refer to the implementation that is automatically rolled out for new installations of UCS as the “standard IDP”. For all releases of UCS 5.0-x, this will continue to be the existing solution with SimpleSAMLPHP, for which you can optionally install the Kopano Connect App for OpenID Connect as in the past.
We plan to switch to the Keycloak App as the new standard IDP with the next minor release, i.e. UCS 5.1. Presumably, with UCS 5.1 it will no longer be possible to continue using the previous IDP based on the old technologies. It is therefore advisable to migrate to the UCS Keycloak app beforehand. With the release of the first version covered by our support now, you can begin now and have enough time to make the switch. An exact release date for UCS 5.1 has not yet been determined, but it is certain that we will provide support and security updates (maintenance) for UCS 5.0 and thus also for the previous IDP for holders of an Enterprise subscription at least until the end of 2023.
We are pleased to introduce the Keycloak App, a significant enhancement to the capabilities and features of UCS. I look forward to hearing your feedback and questions about it – here on the blog, at help.univention.com/, or in person at the Univention Summit on January 17-18, 2023!