We’ve just published the 4th point release of UCS 4.4: apart from bug fixes and some patches, we added some cool new features and improved numerous apps. For example, UCS 4.4-4 introduces logging of LDAP authentications, something that was previously only available via Samba 4. Our developers also put some work into the AD Connector (enhanced security, performance and compatibility), the Univention App Center and the UCS portal login screen. Read on to find out more about the most important innovations.
Logging LDAP Authentications
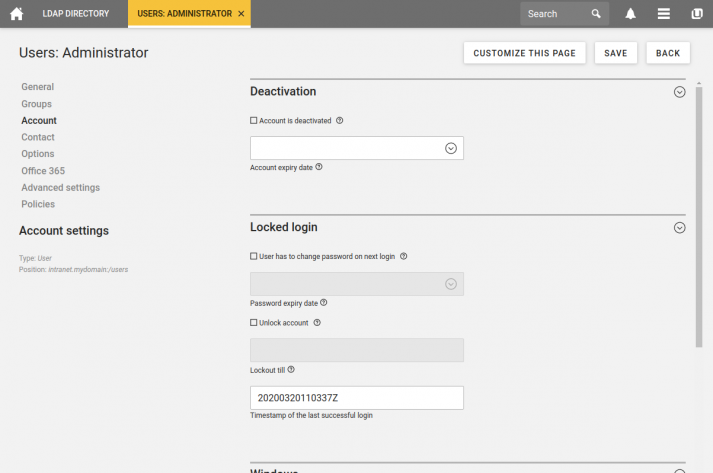
Do you have lots of inactive accounts in your UCS environment that you plan to delete? Did you ever need to find out who was logged in at a certain point in time cause there has been an (unpleasant) incident? Well, we have good news for you: UCS 4.4-4 can now log LDAP authentications (to be precise: LDAP BIND) and display a user’s last login.
For example, if you need to find out when somebody last tried to log in at the SAML IdP, you need to activate the module lastbind overlay in your LDAP servers. UCS 4.4-4 ships a new script that collects the timestamps and saves the most recent one in the user object on the DC Master server. The script can be called manually or via cronjob. Administrators can access the information in the Univention Management Console or evaluate the information in their own scripts.
The new feature is disabled by default, and admins must actively enable logging. Please note that you need to tell your users about the new data collection, and that they have to agree to it. Also, there are two technical points you should keep in mind:
- All LDAP servers in your UCS environment have to be upgraded to UCS 4.4-4 before you enable the feature.
- The load on the LDAP servers will increase, because authentications are no longer just read operations, but also write operations (entries in the database).
Please note that Samba 4 still handles all logins from the Windows/Kerberos environment which means that those logins will appear in different databases than the LDAP authentication.
AD Connector: Windows Server 2019 and Support for Kerberos Hashes
The UCS app Active Directory Connection which is available in our app center connects an existing AD and a UCS domain and automatically synchronizes data between Microsoft Windows Active Directory and Univention Corporate Server. The new version that’s part of UCS 4.4-4 now officially supports Windows Server 2019. Since the connector uses standard interfaces, our development team didn’t have to modify the connector itself, but they added automatic tests and adapted the UCS documentation accordingly.
Synchronizing groups with many members is now a lot faster than in 4.4-3. The AD Connector no longer transfers a full list of all members, but merely synchronizes the changes, e. g. information about new or removed members. While they were at it, our developers also fixed a memory leak in the app.
The most important new feature, though, is the enhanced synchronization of password hashes from a Microsoft Active Directory domain to a UCS domain. It has become much more secure. While the previous version could only synchronize NTLM hashes, the AD Connector of UCS 4.4-4 now also reads newer hashes, the Kerberos keys. The implementation of the new feature was a bit tricky since UCS stores differently hashed passwords in several places and the LDAP directory service must be able to read them. It was also necessary to patch Samba 4 to ensure a successful synchronization.
This new feature is also disabled by default; admins must explicitly activate it. To do this, it is absolutely mandatory to upgrade all systems in the UCS environment to UCS 4.4-4. Otherwise the synchronization will not succeed or users won’t be able to log in.
Download UCS 4.4-4 now
UCS is ready to download as an ISO Image as well as a preinstalled VMware, Virtualbox, Hyper-V and KVM image.
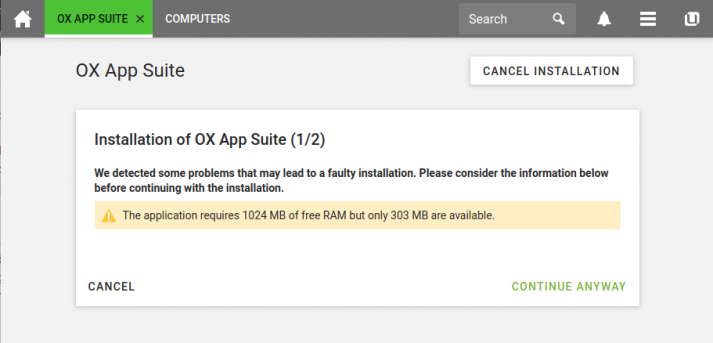
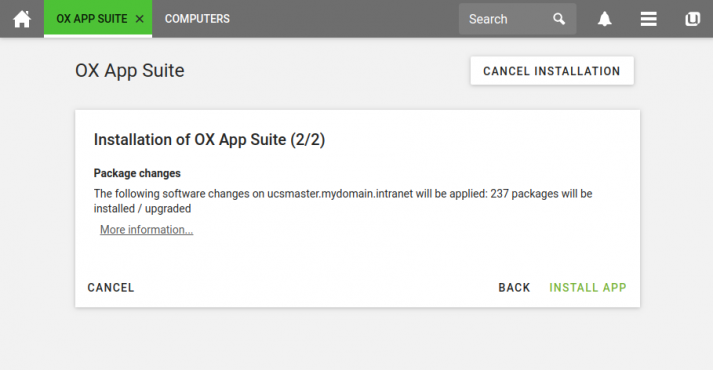
Improved: Installation of Apps, Configuration of the Login Screen
The Univention App Center now starts faster than before and we also enhanced the usability. When admins install a new app, for example, they now receive information about the number of steps required for configuration. The different messages, e. g. the notes of the app manufacturer and the App Center itself, warnings or errors now appear in a uniform, clearer look. In some cases we also combined the messages.
The login screen of the UCS portal offers new configuration options. Administrators can now customize the SAML login links:
- It’s possible to write your own tooltip for the link
How do I log in?and modify the text message. - The link
Forgot your password?takes you to the app Self Service, and users can reset their own password.
Our developers improved the usability in case users want to change an expired password.
List of Corrections: Highlights
So far, we’ve published 499 errata updates for UCS 4.4 since the initial release. The complete list is online, but here are some highlights of the 113 fixes we’ve added since the UCS 4.4-3 release (errata number in brackets):
- Security: bugfixes for Samba 4 (386 und 424), microcode for some Intel CPUs (401), kernel update (480)
- Backend: new check for UMC Check, testing if the UCR variable
ldap/server/namepoints to DC Master (431), random selection of LDAP servers for the script ldap-group-to-file (432, 433), query limit for the Admin Diary has been added (444), activate lastbind overlay module for LDAP (497 etc.) - App Center: the App Center will now check the available disk space before installing an app (392), improved startup performance (405), warnings and errors during an app installation, removal or upgrade are now highlighted and grouped together (419, 455)
- Samba/S4 Connector: more AD Policies can now be synchronized between OpenLDAP and Samba 4 (407), fix for memory leak (422), synchronizing of Kerberos hashes (495)
- AD Connector: group member cache handling has been improved to avoid unbound consumption of process memory (425), filter out users from synchronization (429), synchronizing of Kerberos hashes (494)
- Portal/Login/SAML: link for changing a password in the login screen (408), link
Forgot your password?can be configured (441), linkHow do I log in?on the login page can now be configured (442), Login without Single Sign-On link can now be configured (443), improved SAML session handling (442) - UDM REST API: access to
.../schemaand.../openapi.jsonrequires authentication by default (440)
As you can see, our developers have been busy – at the same time, we’re continuing to work on the upcoming version 5.0. If you have any suggestions for the next major UCS release, please reach out to us via our blog or the forum.