E-mails have become an integral part in our everyday lives. In business anyway, but they have also found their way into our schools. However, schools face the same problems that have long been known by organizations: School authorities with thousands of students, hundreds of teachers and many administrative employees offer hackers a target at least as worthwhile as other large enterprises.
In this article, I’ll show you some simple yet highly effective measures that you as the administrator of a corporate IT or school IT can take to effectively protect your users and mail servers from hacker attacks. As massive spams are not only annoying or even dangerous to us all, they can also cause other mail servers to mistrust your email servers so that your users will no longer be able to send regular mails.
While the corporate world already gained an understanding of the importance of IT security , this is much more difficult with schools. On the one hand, resources for the IT school administration are limited. On the other hand, they haven’t yet fully developed an understanding of IT technology and security standards. Especially, if the users are teachers who consider IT rather as a hobby in the best case, or if these are younger students who will probably be even less aware of the explosive nature of this issue.
![]() So e-mails are a particularly rewarding target since an e-mail server can not only attack the users in the school or company but also all e-mail users connected to them. For a spammer, the sender is not decisive, for him it is only important that his e-mail reaches as many recipients as possible. For this reason, it is particularly important that e-mail servers are protected against unauthorized access and misuse.
So e-mails are a particularly rewarding target since an e-mail server can not only attack the users in the school or company but also all e-mail users connected to them. For a spammer, the sender is not decisive, for him it is only important that his e-mail reaches as many recipients as possible. For this reason, it is particularly important that e-mail servers are protected against unauthorized access and misuse.
Securing the server is not only important to prevent spam e-mails, but also to protect the process of sending official and intentional e-mails. A widespread anti-spam measure is the blacklisting of servers. This means, servers with a high number of sent spam-e-mails are put on a blacklist. The mail servers of other organizations will then no longer accept e-mails from this particular server. So imagine a corporate or school server is misused to send spam and gets blacklisted as a result. Thiswill not only affect the spam e-mails but also all legitimate e-mails sent by employees, students and teachers.
However, a few well thought-out measures can help you to identify and mitigate the problem quickly and cost effectively.
User sensitization – Better safe than sorry
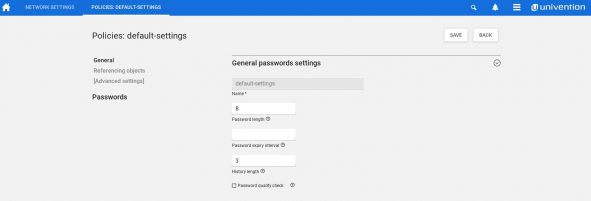
No matter whether in the company, the club, school or in one’s own family, user sensitization always has top priority. It must be made absolutely clear to them to not choose passwords that are too simple or too comprehensible. However, in order to ease this sensitization process, you can define password rules for the use of e-mail accounts in your mail server. For example, you are able to define a minimum of complexity a password must have and determine that the password must be updated at regular intervals. If you are the administrator or teacher of a class, you should, of course, be familiar with these rules so that you can answer questions from your users or students directly.
User authentication – your first line of defense
Thanks to various technical tools, you can do even more than taking these initial basic measures to defend your e-mail servers . Univention Corporate Server has already implemented the most important technical tools for securing e-mails by default.
The first line of defense UCS set up is that only e-mails are accepted that are either intended for a recipient in the domain or sent by a user who has a mailbox in the domain.
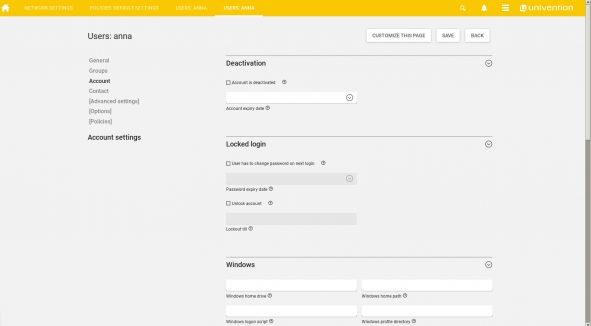
A user who wants to send an e-mail to a recipient outside the domain must first authenticate himself with his password before he can send it. Someone sending an e-mail to an external mailbox via a UCS server simply cannot claim to be the owner of the account, but must prove this first.
Therefore it is extremely important that the password quality is sufficient and no user can log in with ‘1234’ as a password.
Protection against attacks from private devices – your second line of defense
The two measures mentioned above will probably prevent most attempts to use your mail server as a source of spam. However, if you host a large number of users inyour environment using private devices, which is the case in a typical bring-your-own device scenario, you also need to address the problem that the systems of some usershave already been infected by malware. This can be a problem, because malware can use the users’ e-mail-clients for sending spam e-mails. As these e-mail clients run on a valid account, the measures mentioned above will not work. In addition, if a third party is able to access the login information of the respective user, a simple password authentication is no longer sufficient to thoroughly prevent spam. In the article on the protection against ransomware we have already given an overview of many more possible points to attack and defense strategies.
Rule-based systems to detect suspicious email activity – your bastion
However, further measures can also be taken on the server itself to complicate the sending of spam. With so-called “rule-based systems”, you can set up plausibility checks that show whether a real user is sending an e-mail or whether this action is rather dubious. Typical questions to check this probability as an administrator are: “Can this particular user send an e-mail from this explicit location at all?” and “Does the user send an unusually large number of e-mails?“ For example, if an employee or student sends thousand e-mails in five minutes, this would hardly be normal , so the server should block these e-mails. Neither will primary school pupils send e-mails at 2 a.m. or register from abroad during school hours. Nor will one of your local colleagues be sending mails from Hong Kong if your company does not have a branch there and business trips to this region are rather unlikely.
Automatic checks by mtpolicyd daemon – your wonder weapon
All of these checks can be done automatically using a mtpolicyd daemon. The daemon allows you to create a whitelist of countries from which e-mails may be sent. You can also set an upper limit on the number of messages that can be sent per day. Important here: Such a limit will count the number of recipients, not the number of sent e-mails. For example, if the upper limit is 1000 and you want to send an e-mail to 1001 recipients, it will not be possible as you have exceeded your limit by one recipient.
Please find instructions for the setup and configuration of mtpolicyd for UCS in our wiki. We have already successfully set up these packages with customers for UCS Mailstack and Open-Xchange. You can easily integrate further tests via UCR or the configuration.
We are looking forward to your feedback and further suggestions.
Conclusion – your line of defense is set
Rule-based systems make it easier to restrict e-mail dispatch. These policies are instrumental in reducing spam delivery and providing students, teachers, and business users alike with a secure and reliable e-mail system. They thus serve all of us by helping to reduce the number of spam.
The quick and easy installation of a mtpolicyd daemon and the set up with UCR policies can prevent the sending of unsolicited emails by your server.