What is Squid?
Squid is a caching proxy employed primarily for web content delivered via the protocols HTTP, HTTPS, and even FTP. Squid stores websites and their content in a temporary cache, making them available to a number of clients simultaneously. Consequently, the use of Squid makes it possible to speed up the response times when opening websites considerably and reduce data volumes at the same time. In addition to this core function, Squid also boasts other extensive options such as control of users’ access to the Internet (ACLs). This is a scenario which is particularly interesting for use in schools and other public facilities as well as for client authentication. Users and devices are only permitted access to the Internet if they can authenticate themselves against the proxy.
In principle, Squid can be used in two operating modes.
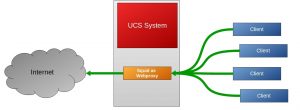
Squid as Web Proxy
Squid as Reverse Proxy
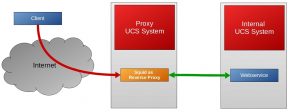
What are the advantages offered by a reverse proxy?
Reverse proxies can increase network security as they make it possible to configure access to web content and the web server is only made available via a defined and controlled intermediate step instead of being placed directly “on the Internet”. In addition, the caching can relieve the strain on the web servers and the reverse proxy can distribute accesses to the websites across multiple web servers in a classic load balancing scenario. Last but not least, Squid in reverse proxy mode can also be used as an SSL end point: All SSL-encrypted connections terminate in the proxy system, which can also relieve the strain on the web servers and, under certain circumstances, allows other options such as effective caching, which might not be possible with encrypted connections.
Where do we use Squid?
As a classic web proxy, Squid is used as standard in UCS@school among others. In such applications, Squid caches frequently visited websites so as to be able to provide clients at the school with a high-performance version. This is a considerable advantage in sites with poorer Internet connections in particular. In addition, user authentication is performed via Squid – in other words, only users with an account in UCS and who can log in are allowed access “to the Internet”. In the case of Squid, the authentication is performed automatically in the background via Kerberos or NTLM – no user interaction is required. In UCS@school, the blocking and approval of Internet sites by means of whitelists and blacklists is effected in cooperation with the complementary software squidGuard.
Together with customers and partners, we have also implemented scenarios in which Squid is used as a reverse proxy. For example, there is a UCS base system with Squid as a reverse proxy connected upstream in an internal wiki. Access from outside is enacted via an external web address, under which the reverse proxy is the first component reached. This terminates the SSL connection – an SSL certificate classified as trustworthy is used – and connects the internally available web server with the wiki installation. In this way, a system which was originally only available internally is now also made available for external accesses.
How do I configure Squid as a reverse proxy?
The basic steps are described in detail in the article Cool Solution – Squid as Reverse SSL Proxy in the Univention wiki.
As soon as the basic functions have been set up, you can begin reproducing different scenarios – you can find helpful example configurations in the Squid project wiki.
