How can companies make access to their networks and applications securer and more user-friendly at the same time? What’s behind the terms SAML, multiple-factor authentication and single sign-on in this context? Cornelius Kölbel, Managing Director of our partner NetKnights, took the time to explain these technologies to us and illustrate how you can use the multiple-factor authentication solution privacyIDEA and SAML to set up a secure network on UCS plus saving employees time when signing in.
SAML
Security Assertion Markup Language (SAML) is a protocol allowing the performance of single sign-on to web applications within distributed networks. At the same time, it is also possible to exchange user information between the different network segments. For this reason it is popularly employed by and between universities and in larger companies with distributed departments.
UCS 4.1
Univention has now integrated SAML in Univention Corporate Server 4.1. The first file UCS 4.1 milestone was released on October 8. In the same step, the UCS domain controller also becomes the SAML identity provider. This allows all apps to delegate the authentication to the SAML IdP (i.e., the UCS domain controller).
For the user this means that he now only needs to sign on to the entire network once and can then use every other SAML-compatible application without the need to sign on again.
This brings with it considerably more security, as the user
- can concentrate more on the single sign-on procedure and protect himself against shoulder surfers
- as well as choosing a longer and safer password, as he only needs to remember one password and enter it one time.
Furthermore, each additional app which connects to SAML represents a mighty quantum leap in terms of usability in connection with the sign-on.
As sign-ons to the network are now focused on this single point, it’s worth making this sign-on even securer. The efforts involved in increasing the security of this single sign-on step on the SAML IdP are also comparatively small.
Multiple-factor authentication
privacyIDEA, an app allowing various different types of multiple-factor authentication, has already been available in the Univention App Center since March 2015. Plug-ins can also be used to expand the sign-on to special apps such as OpenVPN or SSH with a second factor. That means that in addition to the actual password (the “knowledge” factor), the user must also furnish proof of a “possession” factor. Sign-on is only possible if both of these factors are combined correctly.
The idea behind the concept is that the hacking possibilities for the “knowledge” and “possession” factors are very different, and as such the hacking efforts required are considerably higher. Whereas the “knowledge” factor is really easy for the hacker to acquire, an actual physical “possession” factor represents a considerable challenge for a conventional hacker. In case of doubt, the only option is actual physical theft. For this reason, we see using an SMS as a “possession” factor as particularly critical, as an SMS can also be acquired with conventional hacking techniques and without actual physical theft.
In the case of a one-time password token, an apparently random password is generated with a secret key. As only the hardware in which the secret key is encapsulated is capable of generating this random password, the user must consequently be in possession of the hardware.
There are a whole range of different tokens available on the market, all employing different algorithms. In addition, there are also tokens which are integrated in hardware or software. Finally, there are even devices in which the secret key is a proprietary invention of the manufacturer or you can customise the algorithm yourself. privacyIDEA supports all of these different features, so among these varying degrees of freedom you’re sure to find the optimal authentication token for your requirements.
Single sign-on with privacyIDEA
An additional app, privacyIDEA SAML, allows you to expand the single sign-on with a second factor as of UCS 4.1. This requires the installation of a privacyIDEA server on any UCS system in the network. In privacyIDEA, tokens can be assigned to domain users. These can be hardware tokens from different manufacturers. Alternatively, it is also possible to generate software tokens in privacyIDEA. The displayed QR code is scanned with Google Authenticator or FreeOTP.
The privacyIDEA SAML app is now installed on the domain controller which is set to run the single sign-on with two-factor authentication and configured against the privacyIDEA server.
ucr set privacyidea/saml/enable=True ucr set privacyidea/saml/url=https://your.domain.controller.net/privacyidea ucr set privacyidea/saml/verifyhost=True ucr set privacyidea/saml/verifypeer=True
The user now enters his user name for the sign-on. He then enters his static user password in the password field, followed directly by the OTP value generated by his token. Depending on the configuration, the static user password can either be the domain password or a token-specific password.
As of this point, the authentication prompts are sent directly to the privacyIDEA server. This has already been specified in the privacyidea/saml/url variable. In this way, it’s easy to increase the security for all the connected apps centrally and permanently.
Configuration aspects
privacyIDEA offers a wide range of configuration possibilities that are too many to assess in detail in this blog article. Extensive information in this respect can be found in the online documentation.
Here we will only look at two aspects as examples:
It’s possible to control whether the user needs to specify his domain password or a set token PIN as the “knowledge” factor. Using the token PIN makes it possible to protect the domain password in insecure environments. The user can use the PIN and one-time password there in order to avoid revealing the domain password.
userstore policy
Authentication with domain password and OTP
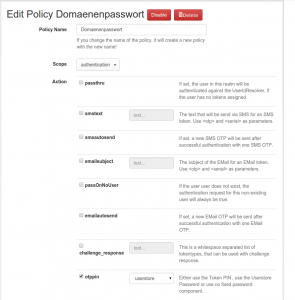
That’s particularly interesting if a second factor needs to be introduced specially for sensitive user accounts. In addition, this function can also be used for a smooth roll-out process.
policy passthru
Without tokens, just one factor
If you require any assistance deciding which are the right tokens for you and how you can use the techniques described here to make your network securer and protect your data, NetKnights with its many years of experience will be delighted to advise you.
Supported token types
privacyIDEA supports a long list of different authentication devices – including in combination with Univention Corporate Server.
- HOTP and TOTP tokens such as the practical SmartDisplayer cards, which can be stored in your wallet.
- HOTP and TOTP tokens such as the eToken NG OTP or eToken PASS, which can be initialized.
- Yubikey for convenient sign-on at the touch of a button. Initialisable.
- Smartphone apps such as Google Authenticator and FreeOTP.
- One-time passwords via e-mail and SMS.
The online documentation contains a complete list of the supported token types.
