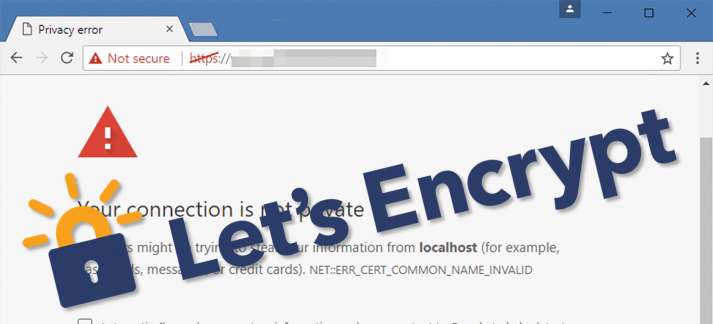
With the announcement of July 23, 2018 at the beginning of February this year, Google created a new milestone on the path to a fully encrypted web. On this day the new version 68 of the Chrome browser will appear, which will, for the first time, mark all websites accessed via HTTP as unsafe. Instead of the well known green lock, which stands for secure HTTPS connections, there will then be shown a grey lettering indicating the uncertainty of the connection.
Indications of the uncertainty of HTTP have been increasing more and more in the past years. With Firefox 52, also Mozilla has integrated a warning message into the browser for login forms on HTTP delivered websites. The aim is to make users aware that their valuable data, such as user name and password, are sent openly legible through the Internet.
In consideration of this development, administrators of web services are increasingly occupied with the question of how a sustainable and cost-effective encrypted access to web-based services can be guaranteed. After all, such an encryption technology requires TLS certificates and the existing certificate issuing authorities take a good amount of money for that.
Our recommendation: Let‘s Encrypt-App
Luckily, we offer the app “Let’s Encrypt” for UCS in the App Center. The app enables the automated retrieval of a free certificate and the setup takes only a few minutes.
a free, automated, open source certificate authority
Launched in 2014 by the Electronic Frontier Foundation, the University of Michigan, and Mozilla, the Let’s Encrypt project recently issued its 100 millionth automated, free certificate and is thus truly living up to its slogan of “Encrypt the entire web”.
In the aftermath of the Snowden revelations of 2013, Let’s Encrypt declared its goal of making SSL/TLS certificates available for everyone on the Internet and promoting free encryption on the web. Since then, the project has won over a wide range of notable companies and acquired sponsors such as Akamai and Cisco as well as most recently Netflix. The project aims to keep the administrative efforts required of the user as low as possible. An HTTPS server should be able to request certificates autonomously with minimal configuration. This maxim also underlies the Let’s Encrypt app for UCS.
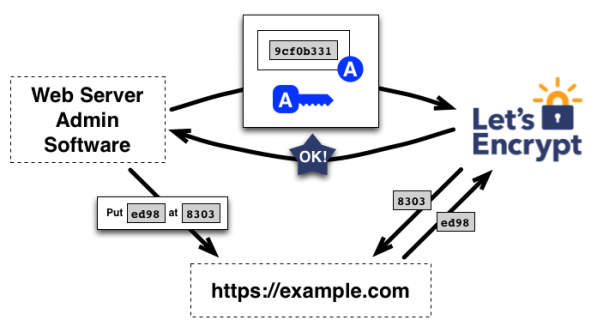
How Let’s Encrypt Works – Automated and Transparent
One decisive aspect of the design of Let’s Encrypt’s infrastructure is a completely automated process for the creation and verification of a requested certificate and complete transparency with regard to these transactions. This makes it possible to view who requested a certificate for which domain at any time so as to avoid abuse.
The technology behind it – ACME-based keys and challenges for the clients
From a technological perspective, Let’s Encrypt is based on the ACME protocol. ACME stands for Automated Certificate Management Environment and was designed for Let’s Encrypt by the Internet Security Research Group (ISRG). It is based on JSON and HTTPS and has already been implemented in clients of various forms.
The ACME client generates an authorized pair of keys for the respective domain in cooperation with the Let’s Encrypt project’s servers. This pair of keys is then entitled to request or revoke a certificate for the domain. If the pair of keys is registered with Let’s Encrypt, the client generates a certificate signing request (CSR), signs it with its key, and sends it to Let’s Encrypt. The Let’s Encrypt servers then select a challenge that the client has to complete. For example, this might be: Save file “x” on your web server with the content “y”. As soon as the client reports that it has completed the challenge, Let’s Encrypt checks whether it has done so successfully (in this case, whether file “x” can be found on the requested domain with the content “y”).
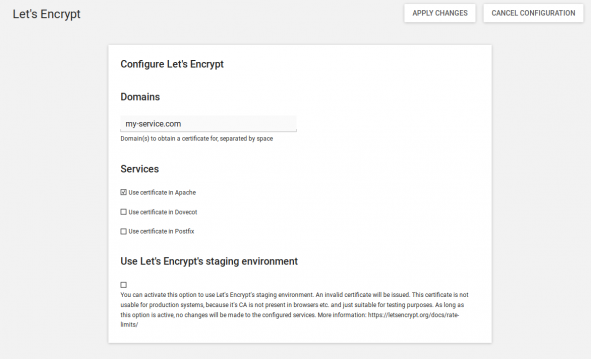
Use the Let’s Encrypt app in UCS to create secure certificates
The Let’s Encrypt app greatly simplifies this procedure and can be installed as usual via the App Center in the web interface. After installation, go to App settings in the App Center to enter the desired domains and configure the use of the certificate in Apache, Dovecot and Postfix.
When you click on “save changes”, a script is started which fetches the certificate and configures it in the respective services. Approx. 10 seconds after clicking on “Save changes” you can see via the status field in app settings whether the certificate was retrieved successfully.
Once the certificate was retrieved successfully, only the configured services must be restarted as a final step. For this, go to the “System Services” module within the “System” category in the web interface. This completes the installation. A cronjob, which is created during the installation will ensure that a new certificate will be obtained every 30 days to always have a valid certificate for the system. This cron job will also restart the configured services automatically.
Use the test environment before going live
The app also offers the possibility to use the staging endpoint of Let’s Encrypt. This endpoint is for testing purposes and should only be used to test the app. A test allows you to ensure that the certificate retrieval and verification of your domain works without a change in the configuration of a service. Simply check the box “Use Let’s Encrypt Test-CA” and click on “Save changes” as usual. In the event of a successful retrieval, the status message also indicates that the certificate is not suitable for production use. After the successful test retrieval, you can undo the check mark and click on “Save changes” again to use the productive endpoint and thus receive a valid certificate.
Once the access to the Apache web server via HTTPS has been successfully configured, it can also be configured to automatically redirect all incoming connections to HTTPS. The verification mechanism of the Let’s Encrypt app is not affected by this.
ucr set apache2/force_https=yes
systemctl restart apache2.service
Do you have any further questions, please leave a comment or visit our forum where our team of experts can help you.
Use UCS Core Edition for Free!
Download nowOpen Source Software Consultant & Engineer in the Professional Service Team at Univention.