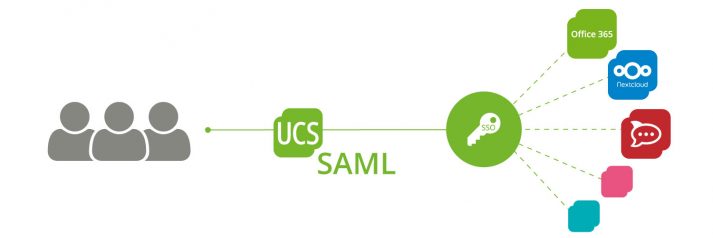
Create an SSO Login for Applications to Groups
Digital Sovereignty is an Indispensable Prerequisite for the Resilience of Our IT Systems – First Lessons from the Corona Crisis
We are in the transition to a “new normal”. However it will look different from the normality before the corona pandemic. Step by step areas of life are being ramped up that until recently were in an unprecedented exceptional situation. This involved a lot of stresses, but it has also brought new and valuable insights into how we can organize our lives. The significance of digital communication options has increased enormously. The use of digital technologies has been accelerated tremendously. It became clear that it is important to have systems that function independently of individual providers or even of foreign countries. Systems that are resilient and can react quickly and effectively to a crisis so that stable conditions can be restored.
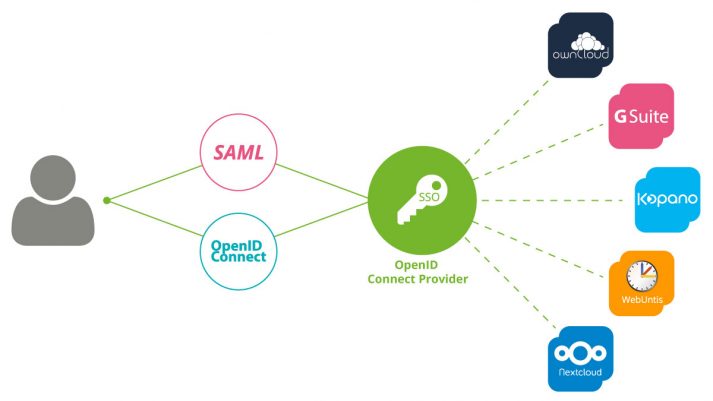
Two Standards But One Common Single Sign-on – Integration of SAML and OpenID Connect
The two authentication standards SAML (Security Assertion Markup Language) and OpenID Connect have already been available to UCS users for some time. So far, however, these two technologies have been two separated worlds. If some of the web services used SAML and others OpenID Connect for the authentication against UCS’ identity management, users were forced to log in twice in those environments with multiple services. With the support of the Kopano team, we were able to release an extension of the app “OpenID Connect ID” in the App Center. This is integrating the two standards with each other and thus allows a single authentication process by the end user.
I would like to briefly explain how a single sign-on generally works with UCS. Then I explain the interaction of Kerberos, SAML, and OpenID Connect and show you which functions the new implementation of Kopano Konnect offers to UCS users.
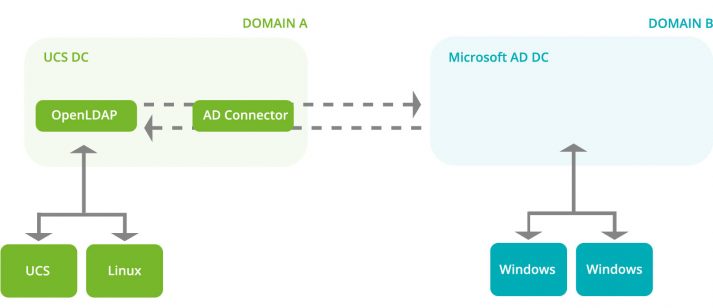
Synchronize Password Hashes between MS Active Directory and UCS
Version 4.4-4 of Univention Corporate Server (UCS) comes with some cool new features, one of them being the new AD Connector app. It makes the synchronization of password hashes between a Microsoft Active Directory domain and a UCS domain significantly more secure and less error-prone. While previous versions could only synchronize NTLM hashes, the AD Connector of UCS 4.4-4 also reads newer hashes, the so-called Kerberos keys which allow single sign-on (SSO) to different applications.
I am a second-year trainee at Univention (job description: IT specialist for application development). I was involved in the development of the new feature and mainly had to deal with three tasks: the AD Connector itself, the OpenLDAP overlay module, and the S4 Connector (Samba). In this blog post I’m going to explain what Kerberos hashes are and how I implemented the new feature.
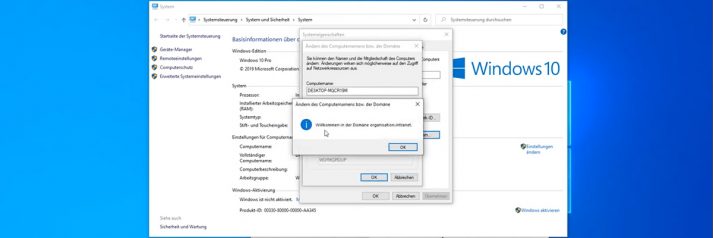
Film Tutorial: How to Add a Windows 10 Computer to a UCS Domain
Setting up an Automatic Account Lockout after Failed Login Attempts
By default, UCS users can enter the password incorrectly any number of times without being locked out by the system. In order to make brute force attacks to crack passwords more difficult, admins can set up an automatic lockout that prevents an account from being accessed after a user-defined number of failed attempts.
Univention Corporate Server offers several methods for authentication and authorization. In this blog article I will show you how to log failed login attempts to the system via PAM stack, OpenLDAP and Samba respectively and how you as an admin can set a limit for the number of unsuccessful logins.
Jitsi Meet and the UCS Identity Management
In recent weeks, the increased demand for video conferencing solutions has kept us in the App Center team busy with the question of how Univention can help companies, organizations and school authorities to communicate effectively in digital form without leaving out aspects of data protection. For this reason, we have intensively studied various open source solutions for video conferencing and published quickly Jitsi Meet as an app in the App Center. It is now available to UCS users for easy installation.
Jitsi is a fully encrypted and 100% open source video conferencing solution. The connection to the UCS directory service via LDAP is already configured. Therefore, administrators of a UCS environment can give users access to Jitsi with their regular username and password using the Univention Management Console (UMC). Then Jitsi can be easily accessed from the UCS portal. In this blog post, I would like to show you the most important installation steps and then focus on the different use cases regarding user authentication. Organizations can use Jitsi Meet on Univention Corporate Server (UCS) to specifically control how open they make the access to the app and which users can conduct video conferences.
Digital Offers for Schools: with Nextcloud, itslearning and Co. through the Corona Crisis – Interview City of Wolfsburg
Being an urban district, our area of responsibility includes 37 schools at 43 different locations. About 1,500 teachers teach a total of 17,000 students at these schools.
Which digital offers are you already using?
We usually have local school server solutions at our schools. We are using iServ at three vocational schools, Logodidact mostly at secondary schools and we still have the MNSPro solution at primary and a few secondary schools. A pilot project was launched four years ago with a council decision. The aim is to test a concept for the implementation of a cross-school solution that is centrally operated and maintained by the school authorities. With the support of the system house Linet Services GmbH that is located in Braunschweig we implemented an identity management system based on UCS@school at six pilot schools with around 5,000 users in 2017. The digital identities of the teachers and students are stored centrally in the identity management system and each user has a uniform user name and password. With these, the users have secure and controlled access via RADIUS to the school WiFi, which is distributed uniformly to all pilot schools. Docked to the IDM of UCS@school we also operate the learning management solution itslearning.