Stubbornness Does Not Suit us: Univention Breaks the Model of Roles for UCS and UCS@school
Let’s Diss Those from the Government!
End of Maintenance of UCS 4.4
Users who are still using UCS 4.4 should update to the more recent version UCS 5 in order to continue receiving security updates, bug fixes and minor releases. In any case, the update sequence must be observed. An update to UCS 5.0 requires at least UCS 4.4-8 with UCS 4.4-8 erratum 972. For more information about the current release versions of UCS 5 and the necessary steps for an update, please refer to the release notes.
Owners of our UCS Standard subscription have the option to sign an extended maintenance support contract for the upgrade from UCS 4.4 to 5. Please contact our sales team at sales@univention.de.
E-mail Archiving: You Should Be Aware of These Misconceptions
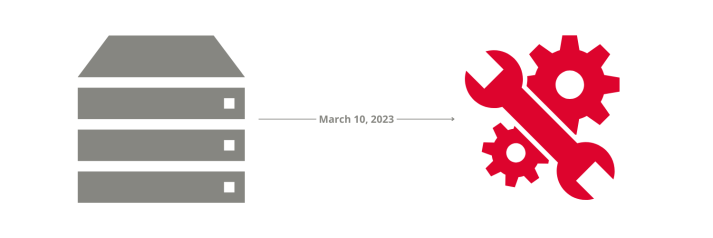
Announcement: Upcoming Maintenance Work on our Servers
On March 10, 2023 we will perform maintenance work on the hardware of various servers. From 5.30 PM to approx. 6.30 PM you will not have access to the following repository servers: