In this brief introduction we want to give you an idea of some important concepts for identity and access management (IAM), and of the related challenges organizations face. We will also see how IAM is one of UCS strengths and why UCS is being adopted by large companies, and by governmental institutions, to manage tens of million identities.
In the real world, we are equipped with the ability to recognize friend from foe, and to decide how much to trust each of them, and despite social engineering, that ability is sufficiently good for our face-to-face social interactions.
 In the digital world, however, the challenge remains to reasonably find out who or what we are interacting with, and how much we should trust them. The challenge gets bigger, the looser the coupling of the network, let it be our home, our workplace, or the Internet.
In the digital world, however, the challenge remains to reasonably find out who or what we are interacting with, and how much we should trust them. The challenge gets bigger, the looser the coupling of the network, let it be our home, our workplace, or the Internet.
Trust is becoming more critical now that many everyday things are getting connected to the Internet and to the company’s network. It is not only people’s and company’s money or property that is getting exposed, but also fundamental institutions for the society (health, public services, elections); and in some cases even our lives.
Now let us briefly go through the core ideas of identity and access management systems.
What is a Digital Identity?
A digital identity is information representing a user or a resource in a specific context. A user is usually a person. Resources can be your computer, the printers in your office, videos and images in a social network, a specific module in an application, etc. A context is where that identity is valid, for example, in your company as an employee or at an ATM as a customer of a bank. More formally, a digital identity is a set of claims (also “assertions”, “known quantities” or “identifiers”) about a person or object within a domain of control, also a federation (see IAM below).
As an example: To enter a country, you may need to request a visa, or register somehow. As part of that process, enough information is collected about you to be able to identify you, for example, a picture, fingerprints, your address, etc. Your identity may include your rights and what access should be allowed (see Authorization below) if such claims are valid (see Authentication below).
What is meant by Authentication?
Authentication is the process of confirming the identity of a person or an object (a so far unknown “subject”) by validating the claims about them (their identifiers) against their digital identity. It is also important to know who is making those claims: Is it yourself answering questions only you are supposed to know, is it your government issuing your ID, or your bank giving your a credit card?
In the real world, we have immigration checkpoints in airports, where someone verifies that you actually are who your passport and your travel documents claim about you. In the same sense, for example, the enterprise directory at your workplace is in charge of validating that you have access to the resources in your corporate network from the password you type or other identifiers, or tokens you show when you log in to your computer.
What is meant by Authorization?
The term authorization comprises the access rights (permissions) of an identity to specific resources. They define how much a user is trusted in a certain context. At work, this would be the resources in the IT network you are allowed to see and interact with. In the airport example, according to the “access policies” of certain country, you will be authorized to stay temporarily as a tourist, or allowed to settle.
Identity and Access Management (IAM)
Sometimes it is simply called identity management (IdM): An IAM System governs the life cycle of identities and their relationships with resources located either in your enterprise network, or in that of your partners, suppliers, or customers. Basically, it means to selectively restrict who has access to what, in which network, how much access they have been granted, and for how long.
It is also possible to control the access by external users to systems or services in a corporate network (also known as federation), or, in contrast, to control the access to external resources by users managed in the local identity provider (IdP in SAML terms). For example, when specific users in your organization are allowed to access certain content in the intranet of your business partner.
The Challenges for Organizations
Organizations need to know who is accessing their data, their devices and their applications and need to control such access. But such control is continually challenged, either by new technologies like cloud computing or BYOD, or by management practices like SoA or Agile to give some examples.
Organizations typically have to govern the access of a few hundred, or of thousands of users to many applications and other resources deployed in different branches, in the network of providers, partners, customers, even in the cloud. Users can also be traveling sales people, or other type of remote workers. Not only that, organizations’ regulations also dictate who should control what information.
Professional IAM with Univention Corporate Server
As an enterprise directory, UCS is centered on the management of information about users, devices, services and other objects, in the organization’s network, that need to be available for the enterprise applications. This includes their complete lifecycle, i.e.creation, replication, authentication, maintenance and removal.
In the first place, UCS creates what is known as a UCS domain, where all the objects are securely managed. Then devices join the domain, user accounts are created or migrated, apps installed and configured, permissions set, etc. For every service, application or resource, integrated to the domain, UCS ensures that the login credentials and account status remain the same for all services. If a password changes, it is updated for all services the account has authorized. If the account is locked, its access to the services will be denied.
Applications in the App Catalog are ready to go right after set up. Our Cool solutions explain how to integrate further software.
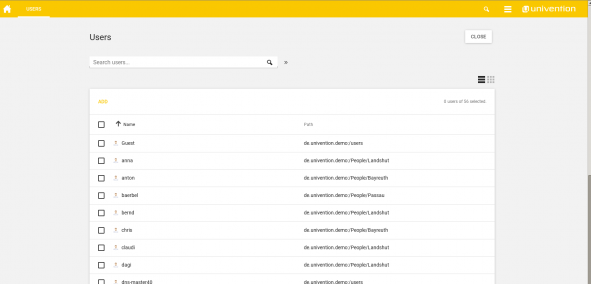
User Management with UCS
Authentication with UCS
The UCS domain uses authentication protocols and mechanisms like Kerberos, LDAP and PAM with both, openLDAP and Samba AD. The domain allows Single Sign-On (SSO) with Kerberos and Samba AD.
For example, different types of user identities are possible for an account in UCS: Samba account (Active Directory user account), POSIX account (UNIX passwd/shadow), Kerberos principal, Simple authentication account (LDAP bind DN) and Personal information (just a contact, with no authentication). They can be chosen at creation.
Here are more examples of how you can improve the authentication process in your network:
- You can allow both federated authentication, and single sign-on for Web applications. Known as Web Single Sign-On (Web SSO) via SAML IdP.
- It is possible to add Two-factor authentication (2FA) and tighten the authentication process.
- A user account can be locked after several failed authentication attempts.
- The different passwords can be set to have an expiry date.
- You can also configure remote authentication of up to thousands of users via RADIUS.
Authorization with UCS
Many options exist to control who has access to what in the UCS domain. For example, only authorized user accounts can login and use the installed applications like OX, Kopano, Egroupware, by activating the option for the account. Also, extended attributes can be used to set your own authorization mechanisms.
UCS can provide services compatible with Microsoft Active Directory, it can integrate with an existing Active Directory. Or it can just take over the MS AD domain.
Many of our Cool solutions describe how to authorize new enterprise applications in the domain, or to authenticate resources. Here are a couple of examples:
- Issue TLS Certificates for your users and computers.
- Automatically login to Vmware vCenter virtual machines (SSO).
User Lifecycle Management
The life cycle of users, groups, Windows and Linux clients or servers, applications, printers, or network shares can be managed in the Web management console UMC (or with the udm command), and it will be replicated across the company’s premises or to the cloud. See all the options UCS has for user accounts. For example, if you click the Account tab for a user in UMC, you can set options for account deactivation, control the login methods, or expiry date after which the account will automatically be locked.
Closing Remarks
In summary, effectively managing identities within the company’s virtual boundaries plus its secure federation to others parties, is crucial if you are responsible for a medium-sized or a large organization that wants to operate safely and successfully in the long term.
We reviewed the IAM features in UCS that let you govern identities for your existing software ecosystem, and let you add value to your users while your IT infrastructure adapts dynamically to the opportunities of the digital world.
Do these features respond to the needs in your organization? Did we miss something important? Please let us know by commenting below. Or have a look at our Forum.
We are looking forward to your feedback!
Use UCS Core Edition for Free!
Download nowOpen Source Software Consultant at Univention